On March 22, 2026, the SERVICE_ROLE key of the Resolv protocol was compromised, resulting in the unauthorized minting of approximately 80 million USR without backing. The attacker accomplished this with only about 300K USDC, securing roughly $23.8 million worth of ETH before exiting.
What deserves more attention than the hack itself is the fact that even after the hack, Morpho's Public Allocator continued to automatically supply USDC to the affected market, providing the attacker with additional exit liquidity. Because a hardcoded oracle still valued USR at $1, borrowing against de-pegged USR continued unabated, ultimately draining an additional approximately $6.2 million in USDC from curator vaults.
Steakhouse, which had been appointed as Resolv's risk manager, published a favorable assessment just days before the hack, stating that the protocol exhibited "institutional rigor." This assessment may have influenced other curators' decisions to expand their market exposure to Resolv. Steakhouse itself had no direct exposure to the protocol, while the vaults of other curators who referenced the assessment suffered real losses.
The fact that it took Resolv approximately three hours to pause the protocol after becoming aware of the hack clearly exposes the limitations of a security framework centered on after-the-fact response. One-time smart contract audits alone cannot defend against operational security threats such as key compromise. It is essential to adopt continuous security frameworks that automatically pause protocols upon detecting anomalies, using real-time monitoring services and additional security layers.
In the early hours of March 22, 2026, the Resolv protocol was hacked. Resolv is a protocol that issues USR, a dollar-pegged stablecoin, backed by crypto assets such as ETH, stETH, and BTC, generating yield through a delta-neutral strategy. Immediately before the hack, the total supply of USR stood at approximately 102 million, and the protocol managed assets worth roughly $141 million.
Source: USR Counter (etherscan)
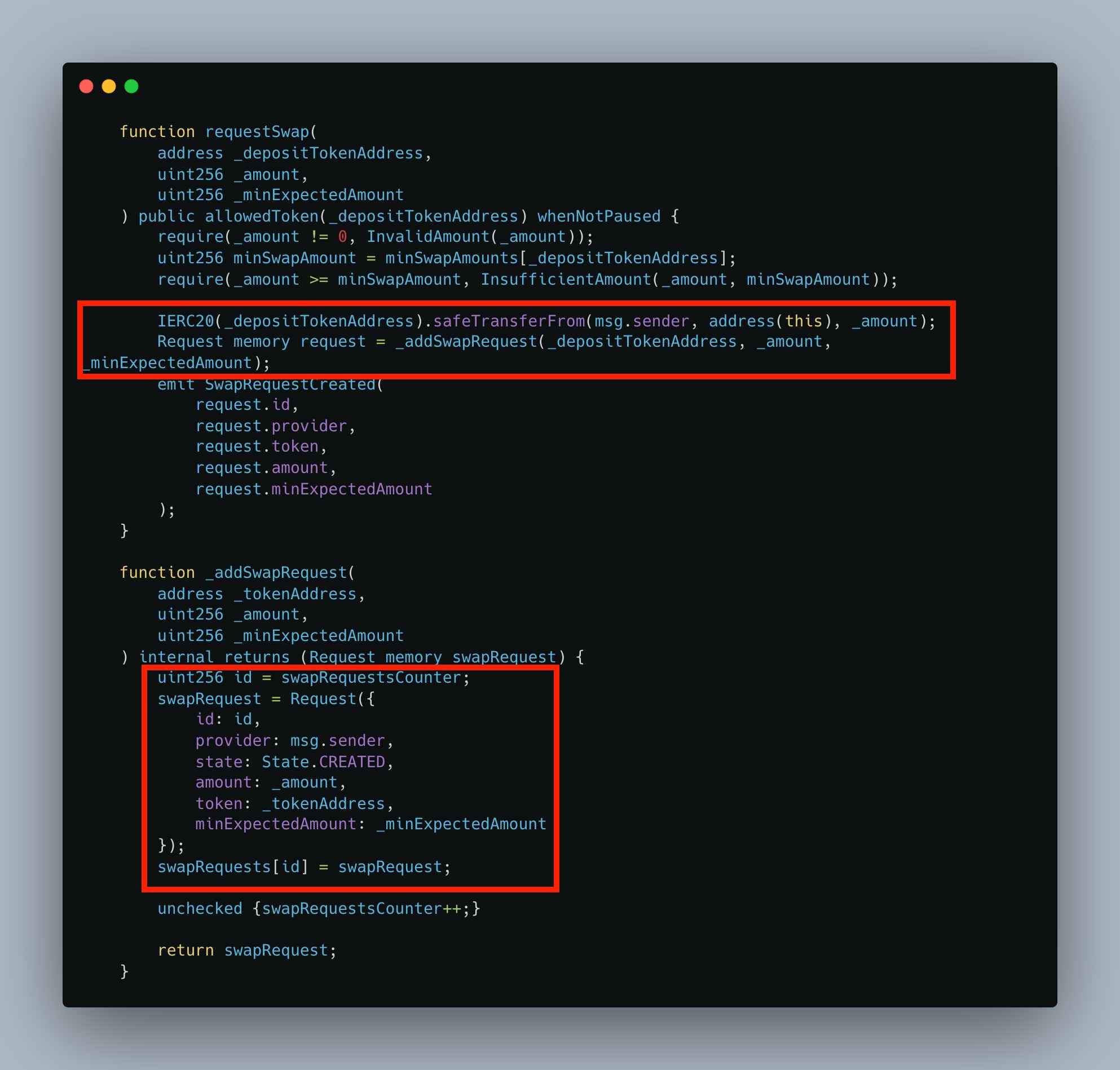
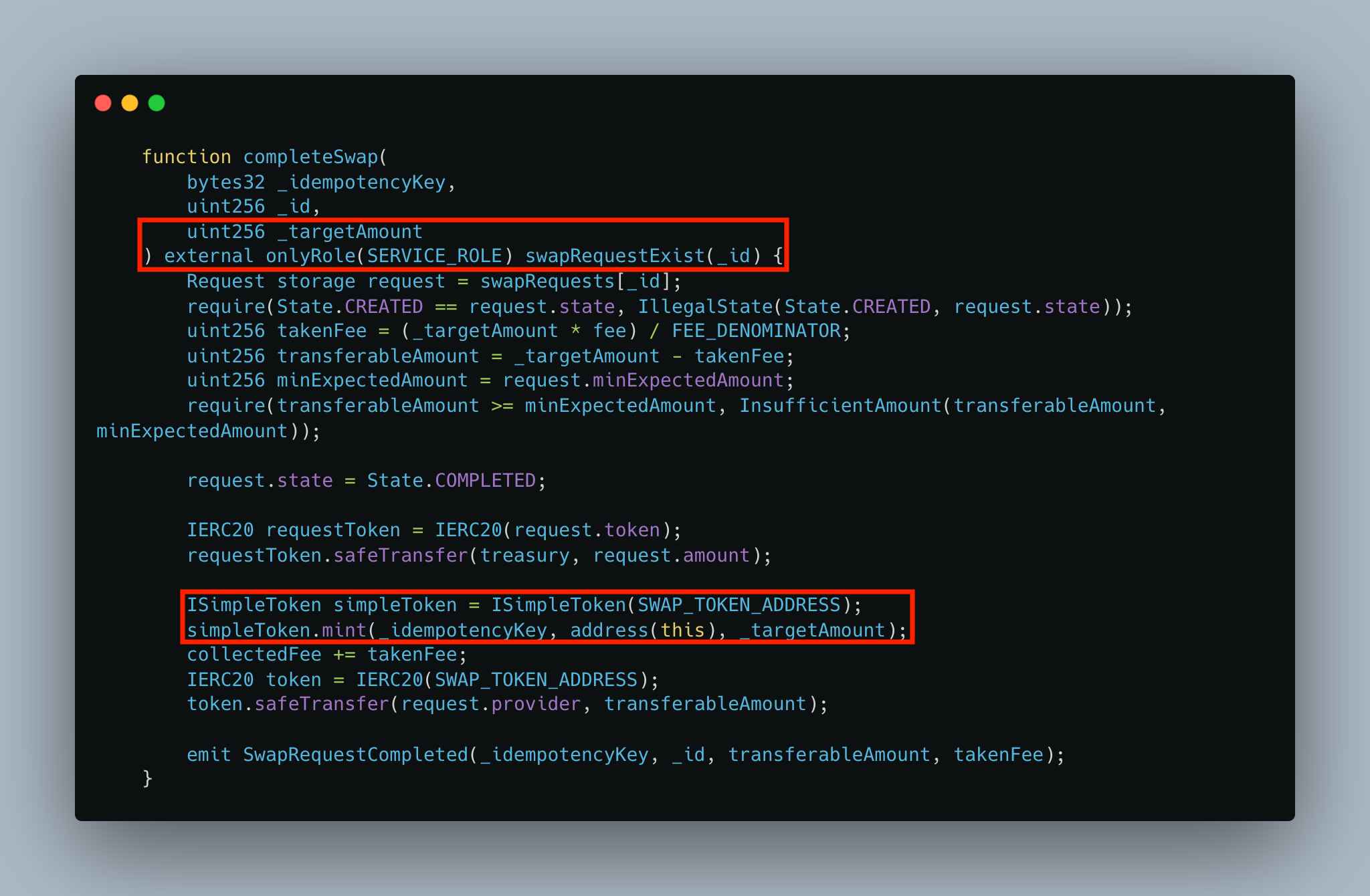
The incident originated in Resolv's minting mechanism. Minting USR on Resolv requires two steps. First, a user calls the requestSwap() function to deposit tokens such as USDC. Then, an account holding the SERVICE_ROLE permission calls the completeSwap() function to determine how much USR to mint. The problem was that this second step involved no onchain verification of the minting amount whatsoever. No logic existed at the smart contract level to verify the ratio between the amount of USDC deposited and the amount of USR to be minted; this determination was made entirely offchain.
Source: USR Counter (etherscan)
The attacker exploited this structural gap using the compromised SERVICE_ROLE key. Onchain records show that the attacker submitted three requestSwap() transactions, each depositing 100,000 USDC. At the completeSwap() stage, approximately 50 million USR was minted for the first request and approximately 30 million USR for the third. With just 300,000 USDC, roughly 80 million USR was created. Notably, the second request (id=31) belonged to a regular user, not the attacker, and in that case only about 100,000 USR was minted as expected. This detail demonstrates that the attacker was able to manipulate the system selectively.
The unbacked USR was quickly liquidated. The attacker primarily dumped large quantities of USR into the Curve Finance USR/USDC pool to convert it to USDC, then swapped the USDC for ETH. According to onchain data, the attacker is estimated to have secured approximately 11,400 ETH (worth roughly $23.8 million). USR's price plunged to between $0.14 and $0.25 depending on the source (briefly dropping as low as $0.025), and while it later recovered to around $0.42, the dollar peg had been completely broken.
Resolv Labs was only able to pause the protocol approximately three hours after the incident occurred. A significant portion of this delay was attributable to the process of collecting multisig signatures. The fact that it took about one hour just to gather the four required signatures after the pause transaction was submitted supports this point. Resolv stated that the underlying collateral assets themselves were not compromised and that the damage was confined to the USR minting mechanism. It announced that redemptions for USR issued before the hack would begin on March 23.
The root cause of this incident is relatively straightforward. The SERVICE_ROLE, which held minting authority over tens of millions of dollars, was assigned to a single EOA (Externally Owned Account), meaning an account controlled by a single private key.
In other words, possession of one private key was enough for complete control. The fact that Resolv's protocol pause function was protected by a multisig, while the core authority governing asset issuance relied on a single EOA, represents a clear imbalance in security design.
Beyond this, the complete absence of onchain guardrails cannot be overlooked. The minimum safeguards that a protocol of this nature should typically have in place include: a per-transaction mint cap, a ratio check between deposit amount and minting amount, an oracle price guard for cross-verifying minting volume, and enforcement of a user-specified minimum expected amount (minExpectedAmount).
None of these were implemented in the completeSwap() function. The account holding the SERVICE_ROLE was effectively granted unlimited minting authority without any constraints.
The most noteworthy aspect of this incident is not the hack itself, but the process by which Morpho's automated liquidity allocation mechanism activated after the hack and amplified the damage. To understand this amplification mechanism precisely, however, the layers of causation must first be distinguished.
The amplification resulted not from a single cause but from the combination of three factors.
First, the failure of the hardcoded oracle served as a necessary condition. Had there been no oracle still valuing de-pegged USR at $1, the borrowable amount would have been proportionally limited to actual market value, even if USR trading at $0.14 to $0.25 was deposited as collateral. If the oracle had correctly reflected market prices, no amount of liquidity supplied by the Public Allocator would have enabled bad loans, because collateral would have been accurately valued.
Second, the Public Allocator functioned as a multiplier of the damage scale. If the oracle failure opened the possibility of bad loans, the Public Allocator expanded the total pool of capital available for that possibility to be realized. Had only the liquidity already deposited in the affected market been available, the damage would have been confined to that amount. But by pulling in liquidity from other vaults, the Public Allocator expanded the damage to $6.2 million.
Third, arbitrageurs actually exploited this structure by executing borrows. The Public Allocator supplied liquidity; it did not force anyone to borrow.
This distinction matters because it directly affects the prioritization of countermeasures. Adding safeguards to the Public Allocator is necessary, but improving the oracle so that it reflects real-time market prices even under extreme conditions is the more fundamental solution, as it would prevent bad loans from arising in the first place.
With the causal structure understood, let us examine the actual mechanics.
Morpho is a decentralized lending protocol with an isolated market architecture. Each lending market consists of a single collateral asset and a single loan asset, designed so that risk does not propagate between markets. Above these isolated markets sits a layer called MetaMorpho Vaults, which function like funds that distribute capital across multiple markets to provide depositors with optimized yields. The allocation of capital within these vaults is managed by entities known as curators.
The Public Allocator was introduced to solve the liquidity fragmentation problem within this vault structure. Morpho's isolated market architecture provides the important advantage of risk isolation, but it comes at the cost of liquidity being fragmented across individual markets. When borrowing demand surges in a particular market, interest rates spike while idle liquidity sits unused in other markets. The Public Allocator resolves this inefficiency by allowing anyone to call it to redistribute idle liquidity from other markets into the market where demand exists. This function, which improves depositor yields and reduces borrower costs, plays a critical role in the capital efficiency of DeFi lending protocols. Since it operates only within limits (flow caps) preset by curators, safeguards are theoretically in place.
Examining how this mechanism operated during this incident, however, reveals an outcome diametrically opposed to its design intent. The same mechanism that enhanced capital efficiency under normal conditions transformed, during a crisis, into a channel propagating one market's bad debt into other vaults. The Public Allocator effectively neutralized the risk isolation benefit provided by the isolated market structure.
After USR de-pegged, arbitrageurs purchased USR at its crashed market price, deposited it as collateral in Morpho's wstUSR/USDC market, and borrowed USDC by exploiting the hardcoded oracle that still valued USR at $1. As borrowing demand surged, the Public Allocator was triggered, and USDC began flowing automatically into this market from the vaults of multiple curators, including Gauntlet.
According to the analysis by Chaos Labs founder Omer Goldberg, prior to the hack at approximately 2:20 AM UTC, outstanding USDC borrowed against USR collateral in that market totaled only about $4,900. But after Gauntlet's automated allocation began at 2:41 AM, a pattern repeated over roughly 90 minutes in which borrowers executed borrowing requests immediately after each allocation. Some curators recognized what was happening and stopped, but others, such as 9summits, continued supplying for approximately 10 hours. In total, approximately $6.2 million in USDC was additionally supplied to the affected market through curator vaults after the hack, with 96% of this amount flowing from Gauntlet's vault.
This raises a critical design question: what balance should the Public Allocator strike between capital efficiency under normal conditions and risk propagation during crises? Removing the mechanism is not the answer, as its value during normal operation is clear. The realistic alternative is adding conditional safeguards, specifically circuit breakers that detect abnormal conditions. For example, logic could be considered that pauses automated reallocation to a given market when the utilization rate within that market spikes sharply in a short period, or when a meaningful discrepancy is detected between an asset's external market price and its oracle price. This approach would preserve efficiency under normal conditions while blocking damage propagation only in extreme scenarios.
In conclusion, it is more accurate to evaluate the Public Allocator not as a fundamentally flawed design, but as an incomplete design lacking safeguards for extreme conditions. The focus of criticism should be not on the existence of the function itself, but on the absence of safety mechanisms that would automatically halt it during a crisis.
As described above, $6.2 million in additional outflows occurred after the hack, but a particularly notable data point is that under the same Public Allocator system, curator responses varied dramatically. Some curators recognized the anomaly and halted supply, while 9summits continued supplying for approximately 10 hours. Furthermore, 96% of the outflows came from Gauntlet's vault.
This data admits two contrasting interpretations.
From a system design perspective, the fact that outflows continued from other curator vaults even after some curators responded immediately suggests that a structure dependent on individual curator capability is inherently fragile. The speed of the slowest responder determines the vulnerability of the entire system. From an operational capability perspective, the fact that outcomes differed among curators using the same system indicates that the key variables determining the scale of damage were differences in operational standards: monitoring frameworks, response processes, and the conservatism of flow cap settings, rather than the system itself.
Additional analysis is needed to understand why Gauntlet accounted for 96% of the outflows. Whether Gauntlet had set the largest flow caps, managed the most vault assets, or was particularly slow to respond changes the implications. If Gauntlet's flow cap settings were excessively generous relative to other curators, this is closer to a problem with Gauntlet's risk parameter configuration than a design flaw in the Public Allocator.
Why, then, had so many curators enabled automated supply to Resolv-related markets? This is where the role of risk assessment warrants examination. In the DeFi ecosystem, Steakhouse Financial is one of the leading risk curators and also the largest vault curator in the Morpho ecosystem. Steakhouse had recently been appointed as Resolv's risk manager, and according to Goldberg, it published a risk assessment report on Resolv just days before the hack.
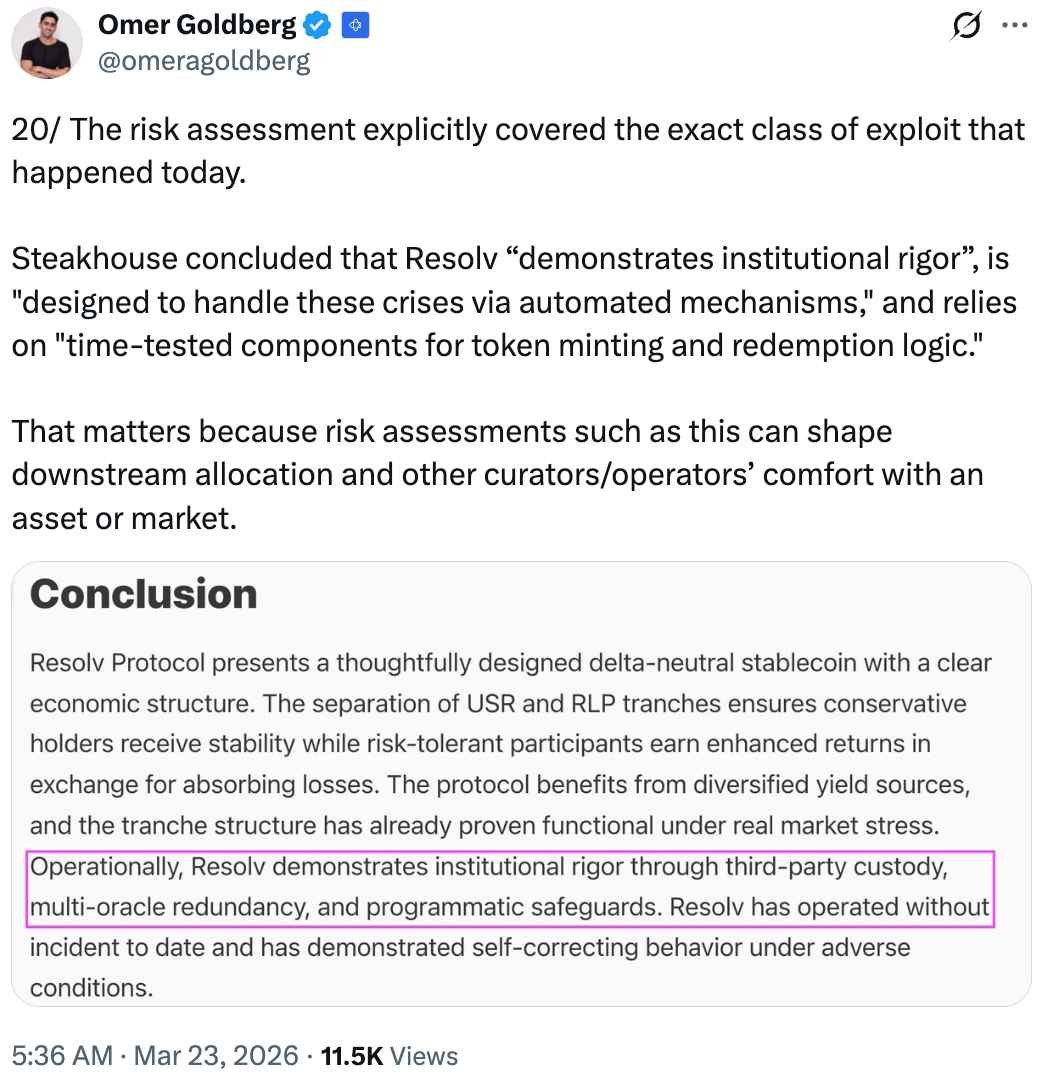
Source: @omergoldberg
The report itself was a technically thorough analysis. It covered in detail Resolv's two-token structure, the mechanics of the delta-neutral strategy, the risk distribution between USR and RLP, and the operation of collateral pools. However, while the report addressed the very type of attack that actually occurred, it concluded that Resolv "demonstrates institutional rigor," is "designed to handle crisis situations through automated mechanisms," and "uses verified components in its token minting and redemption logic."
The downstream impact of such assessments should not be underestimated. Risk assessments serve as direct reference material when other curators and operators decide on their exposure to a given asset or market. If a highly trusted risk curator such as Steakhouse issued a favorable assessment of Resolv, it may have influenced the decisions of other curators, including Gauntlet, Re7, kpk, and 9summits, to enable automated supply to Resolv-related markets.
This is not to say that risk assessments should predict every future incident, and it would be difficult to conclude outright that the quality of analysis in Steakhouse's report was deficient. Still, the question remains as to whether, in addressing operational security risks such as "key compromise" or "infrastructure breach," the report sufficiently verified the protocol's actual security implementation.
USR's de-pegging did not remain contained within the Resolv protocol. This is because USR and its derivative token wstUSR, along with the risk-absorbing token RLP, were being used as collateral across multiple DeFi lending protocols. Centered on Morpho, numerous protocols were affected, including Euler, Fluid, Lista DAO, and Inverse Finance. On Morpho, approximately 15 vaults showed meaningful levels of exposure. After the hack, USR's market value plummeted, but the hardcoded oracle continued to value USR at $1. As a result, lending positions effectively became unsecured, generating bad debt.
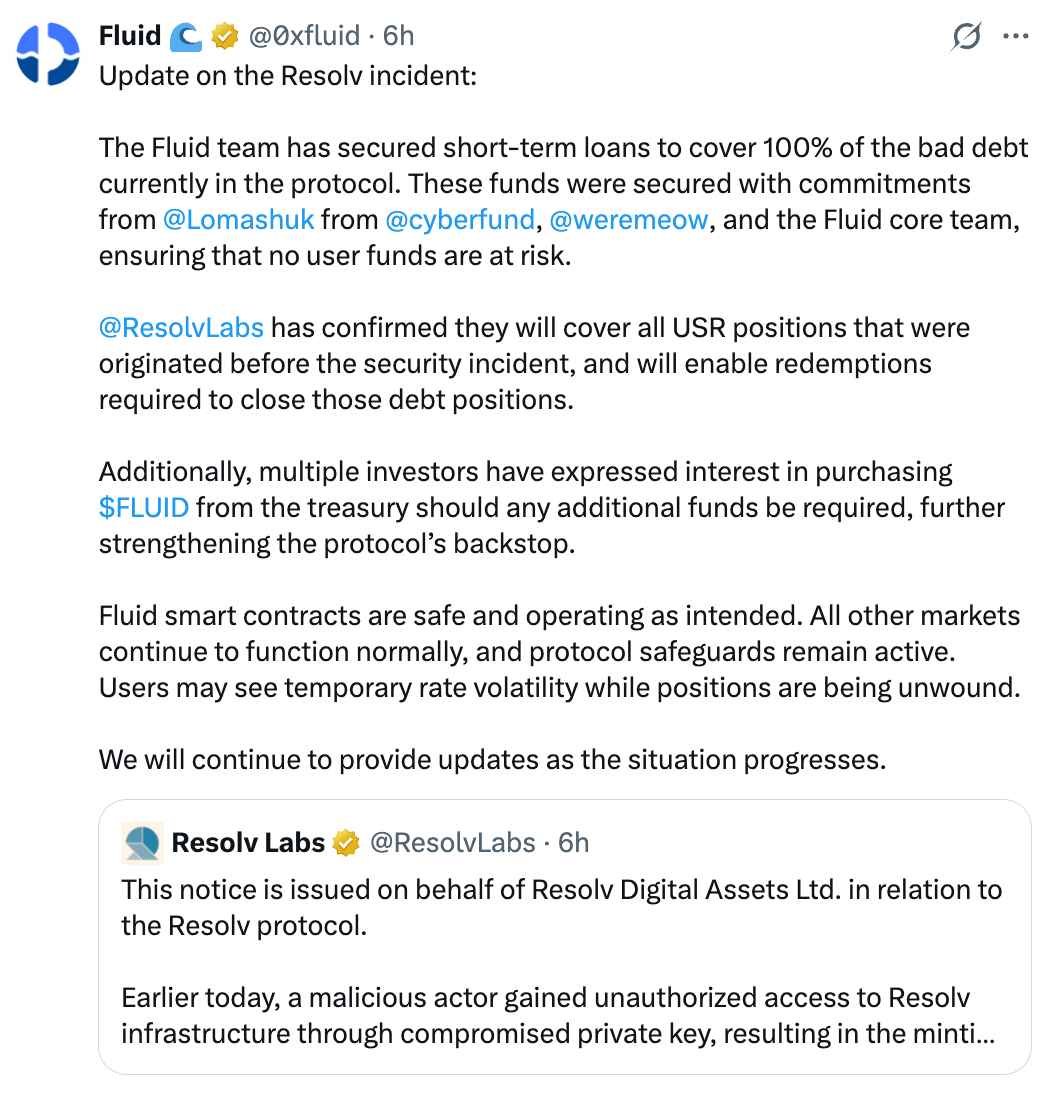
Source: @0xfluid
Among protocols outside of Morpho, Fluid suffered the largest losses in this incident, with potential damages estimated at over approximately $11 million. The Fluid team announced that it had secured a short-term loan to cover the full amount of bad debt within the protocol. Lomashuk and weremeow from Cyberfund, along with the Fluid core team, participated in securing the funds, and they stated that user funds would not be put at risk. According to Fluid, Resolv Labs confirmed that it would cover all USR positions issued prior to the security incident and enable the redemptions necessary to liquidate the corresponding debt positions. Should additional capital be needed, multiple investors have expressed willingness to purchase $FLUID tokens from the treasury.
Fluid co-founder Samyak Jain stated through community channels that the protocol treasury holds at least $6 million in assets, and that even in the worst case, losses could be covered by selling tokens to partners and investors at a modest discount with short-term lockup conditions. He indicated that raising $10 to $20 million would not be a major issue and that the protocol had not sustained an irrecoverable blow.
However, $11 million is by no means a small loss. Treasury assets of $6 million alone cannot fully resolve the bad debt, and if the scenario of selling $FLUID tokens from the treasury at a discount materializes, the cost is ultimately borne by retail token holders who hold $FLUID on the open market. When a large volume of tokens is released at discounted prices, existing holders see their stakes diluted and selling pressure intensifies. The statement that "user funds are not at risk" means that depositor (lender) principal is preserved; it does not mean that the value of protocol token holders is protected. In effect, protocol-level bad debt is socialized onto retail holders through token dilution.
Fluid's response was relatively swift, and the availability of multiple funding channels demonstrated short-term crisis management capability. At its core, however, this is an after-the-fact cleanup reliant on the team's network and credibility, which also reveals the limitation that it is a recovery approach far removed from the trust minimization that DeFi aspires to.
Source: @InverseFinance
In the case of Inverse Finance, the Risk Working Group (RWG) paused the wstUSR-DOLA FiRM market within 15 minutes of the initial exploit. At the time, approximately $10 million in DOLA debt existed in that market, collateralized by looped wstUSR-DOLA LP positions. Liquidators fully liquidated these positions, limiting the final residual bad debt to approximately 340,060 DOLA. Inverse Finance stated that DOLA's broad collateral base was not materially affected and that the incident had been fully contained.
Inverse Finance's case provides a noteworthy reference point among the responses to this incident. Compared to Resolv itself, which took three hours to pause the protocol, Inverse Finance halted the relevant market within 15 minutes. And despite the existence of $10 million in debt positions, the liquidation mechanism functioned as intended, containing bad debt to the $340,000 level. This stands out as an example of effective crisis response.
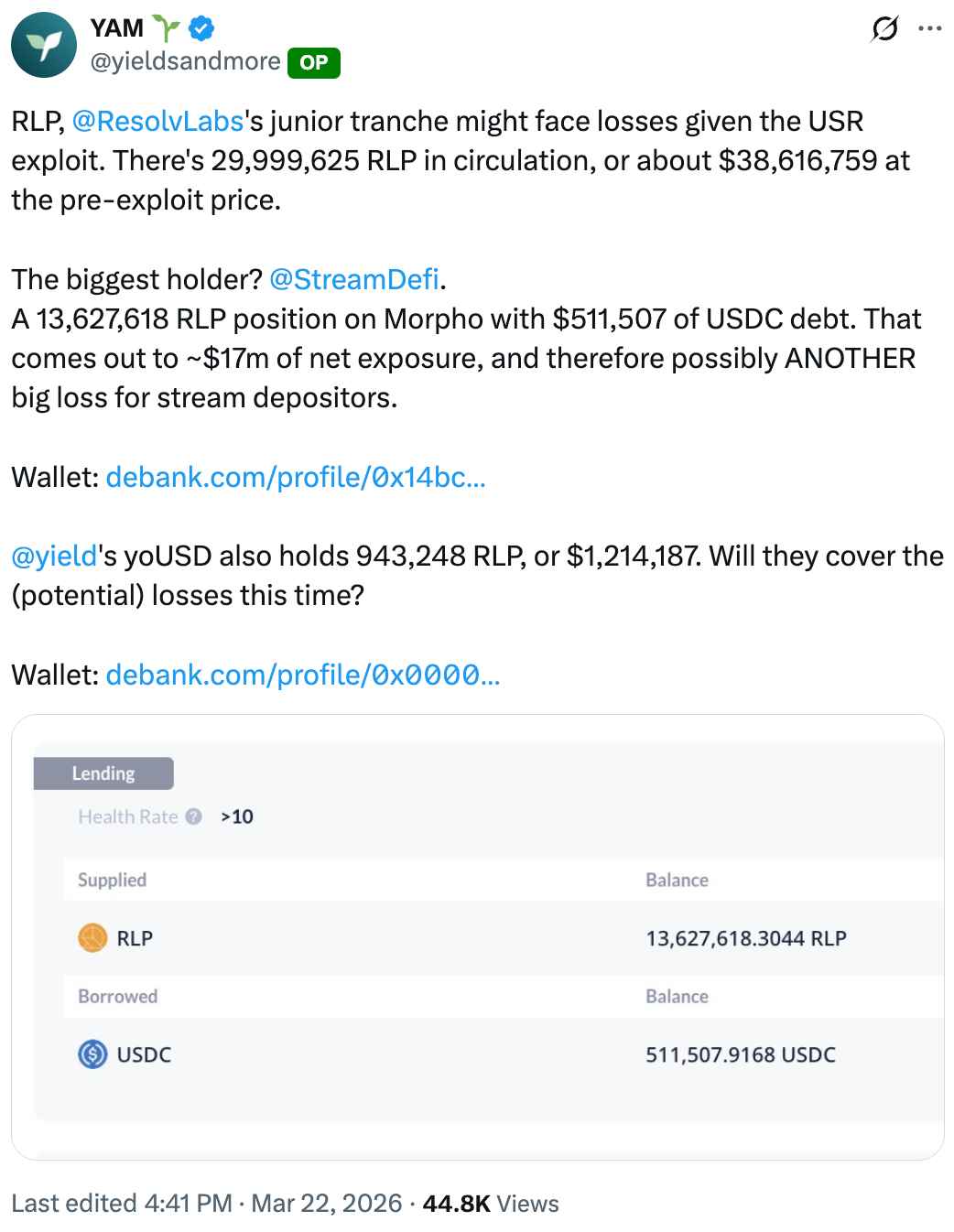
Source: @yieldsandmore
The situation at Stream Finance adds further concern. Stream Finance is a yield protocol that disclosed approximately $93 million in losses in November 2025 due to asset misappropriation by an external fund manager. Stream held approximately 13.6 million RLP tokens on Morpho, representing a net exposure of roughly $17 million at pre-hack prices. RLP serves as the junior tranche in Resolv's structure, a concept from structured finance referring to the subordinate layer that absorbs losses first when they occur. In Resolv's case, RLP holders bear losses ahead of USR holders to protect the latter. Given this, Stream's depositors may face significant losses yet again within just a few months.
This incident leaves several lessons behind.
I have repeatedly emphasized that the security of blockchain protocols cannot be ensured through smart contract audits alone, and has argued that continuous monitoring systems, rather than discrete audits, are essential for comprehensive security. The fact that it took Resolv three hours to pause the protocol serves as yet another case reinforcing the necessity of such systems.
YieldsAndMore, who covered this incident in depth, proposed that "emergency pauses should be executable with a single signature, and this authority should be distributed across as many team members as possible." YieldsAndMore also noted that proactive monitoring services such as Hypernative and Hexagate could be used to automatically pause protocols upon anomaly detection.
Beyond this, I would like to stress the need to redefine the role of curators. In DeFi's modular lending architecture, curators are not simply automated allocators optimizing for yield. They are entities that exercise judgment over the allocation of capital, and they collect fees for doing so. If a curator's risk curation fails to intervene in a timely manner during a crisis, the system is in practice no different from an automated allocator sitting atop a smart contract with a pause button, collecting fees.
An additional point that warrants discussion is the attitude of projects toward admin key compromise scenarios. Most projects treat attack scenarios that require the compromise of admin privileges as "out of scope" during security audits or bug bounty programs. Operating under the assumption that administrators are trusted entities, they exclude scenarios involving the abuse of such privileges from review. However, as this incident clearly demonstrates, admin keys can be compromised, and in this case, they were. Failing to implement layered defense mechanisms that can limit damage even when admin privileges are breached, such as mint caps, timelocks, and ratio checks, amounts to design negligence.
Source: @ZeroK_____
Indeed, even after the Resolv hack, cases have surfaced within the security community of researchers who reported similar admin privilege-related vulnerabilities, only to have their submissions dismissed on the grounds that "admin privileges operate under a trust assumption and therefore do not constitute a valid vulnerability." A security model built on the premise that "administrators can be trusted" is nothing more than a single point of failure, one that, the moment the premise is violated, brings everything down with it.
One of the core values that DeFi pursues is trust minimization: building a transparent and verifiable financial system by trusting code instead of intermediaries. Yet the Resolv case vividly demonstrates how easily this promise can be undermined. When unchecked onchain authority, automation that fails to function properly in a crisis, and risk assessments divorced from actual security implementation converge, user assets remain unprotected no matter how decentralized a protocol claims to be.
Security architecture should be designed not with the goal of "a system where hacks never happen," which is virtually impossible to achieve, but rather "a system where damage is minimized when hacks do happen." This demands not merely passing a smart contract audit but a comprehensive approach encompassing key management frameworks, onchain guardrails, emergency response processes, safeguards within automated systems, and the substantive rigor of risk assessments. I hopes this incident can catalyze such a shift in awareness across the industry.
Dive into 'Narratives' that will be important in the next year