Lido's existing emergency pause mechanism, GateSeal, required annual redeployment due to its single-use design, and as the number of protected contracts grew beyond ten, the operational burden compounded.
CircuitBreaker eliminates the redeployment burden while preserving GateSeal's security properties through three design choices: a permanent address, independent per-contract permission management, and heartbeat-based proof of committee liveness.
CircuitBreaker serves as a governance design case study in how a decentralized protocol can structurally reduce the operational cost of an inherently centralized tool like emergency pausing.
The fact that no one can arbitrarily stop a smart contract once deployed is both its greatest strength and its greatest weakness. Under normal conditions, this provides the value of liveness. But when a critical bug or hack occurs, damage spreads in real time with no way to respond immediately. To address this, most crypto projects have implemented mechanisms that pause core functions when anomalies are detected.
The question of who gets to press the pause button, however, can become extremely thorny depending on how decentralized the protocol is. Governance votes take days; delegating authority to a specific individual introduces centralization risk. Lido's compromise has been GateSeal, a single-use emergency pause contract that can be triggered when a multisig committee reaches consensus. Then today, April 9, a proposal was posted on Lido to replace the existing GateSeal with a permanent mechanism called CircuitBreaker.
Source: Lido
This article covers the background behind CircuitBreaker's emergence, the details of its implementation, and the broader implications it leaves us with.
GateSeal's operating principle is easiest to understand through an analogy with an electrical fuse. When excessive current flows in a household circuit, the conductor inside the fuse melts and protects the circuit, but a blown fuse must be replaced with a new one. GateSeal follows the same pattern. Once triggered in an emergency, it expires immediately. Even if never triggered, it automatically expires after a maximum lifespan of one year. The committee can selectively pause only some of the registered contracts, but regardless of what they choose, the GateSeal itself expires immediately. For example, if only 2 out of 8 registered contracts are paused, and the committee later wants to pause the remaining 6, the already-expired GateSeal cannot do so.
Whether expiration comes from triggering or from the passage of time, the same cycle must repeat: deploy a new instance, undergo a security audit, hold a Snapshot vote, then run an on-chain vote to revoke pause permissions from the old instance and grant them to the new one. This was a deliberately inconvenient design, intended to pressure the DAO into building a better, permanent solution.
At the time of Lido V2, GateSeal protected only two contracts, and renewal was annual, so the operational burden was manageable:
WithdrawalQueue: handles the stETH → ETH withdrawal queue for users
ValidatorsExitBus: the validator exit bus for node operators
But three years later, the following upgrades have been introduced to Lido, significantly expanding the scope of what needs protection:
Lido V3: introduction of stVaults for custom staking
Triggerable Withdrawals: a framework for the DAO to directly trigger validator exits
Dual Governance: a mechanism granting stETH holders veto power over DAO decisions
Community Staking Module: a module enabling participation by individual stakers
As a result, the number of contracts requiring emergency pause capability has grown to over ten, managed across four separate GateSeals. This means repeating the deployment and verification process for each one every year.
There is also a more fundamental problem. Between the moment a GateSeal expires and the moment a new GateSeal's on-chain vote is finalized, a gap can emerge during which no emergency pause mechanism exists. Looking at the April 2024 renewal, the margin between the existing GateSeal's expiration date (May 1) and the vote completion date (April 26) was only a few days. As the protocol grows in scale, this kind of tight schedule becomes an increasingly serious risk factor.
CircuitBreaker is, as the name suggests, analogous to the circuit breaker in your home's electrical panel. Unlike a fuse, a breaker trips when overcurrent occurs but can be reset by flipping the lever once the problem is resolved. The CircuitBreaker contract follows the same pattern. Once deployed, it exists permanently, and after being triggered, it can be reused once the DAO re-grants permissions.
There are three core design elements to CircuitBreaker.
The first is a permanent address. CircuitBreaker is a single contract whose address never changes. The DAO only needs to grant each pausable contract the permission "this address can pause you" once. The annual renewal procedure from GateSeal, revoking the old instance's permissions then granting them to the new one, is eliminated entirely.
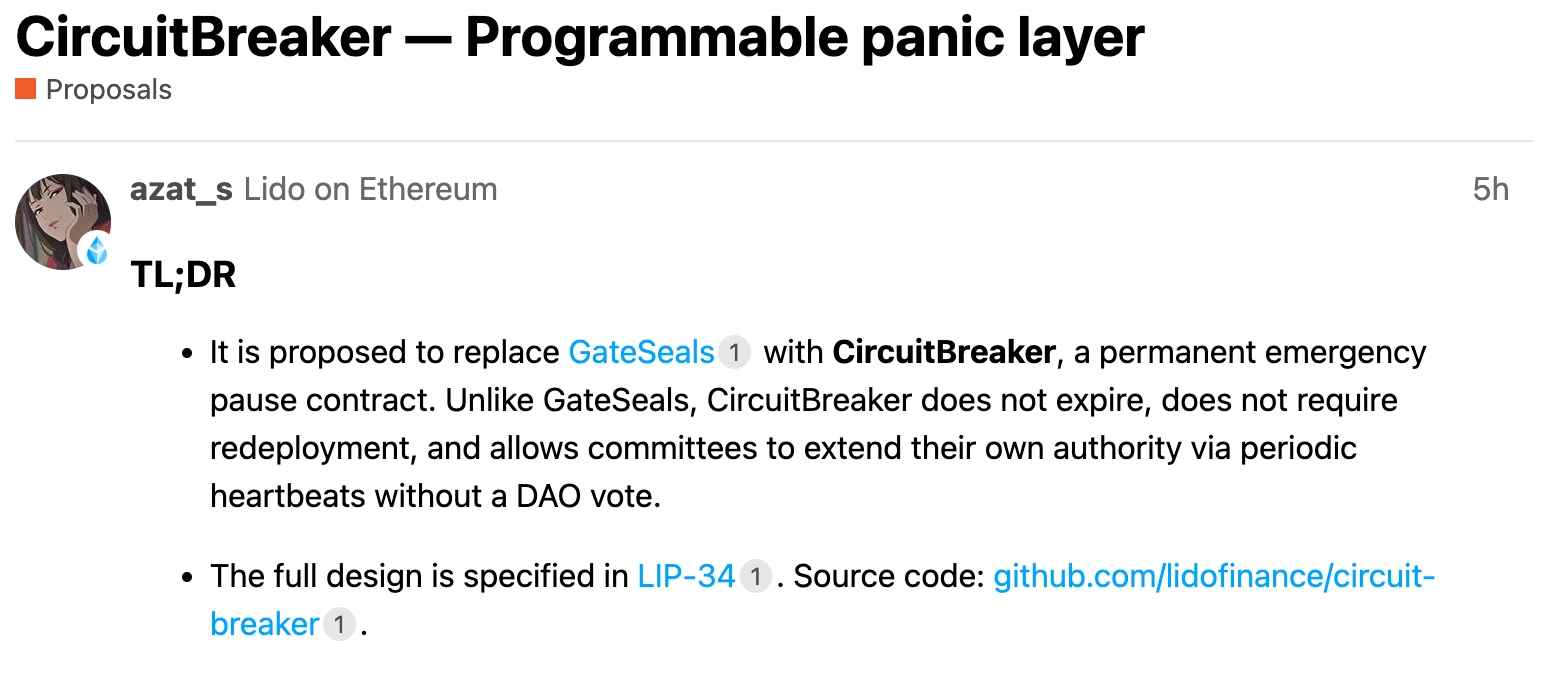
Source: Lido
The second is a single-use pause mechanism. When the committee triggers a pause on a specific contract during an emergency, CircuitBreaker pauses the target and then immediately revokes the committee's permission over that contract. If the committee wants to pause the same contract again, it needs reauthorization from the DAO. This directly inherits the single-use property that was GateSeal's core safety feature. The critical difference from GateSeal, however, is that pausing one contract leaves permissions for all other contracts intact. Under GateSeal, even a partial pause caused the GateSeal itself to expire, stripping the ability to respond to remaining contracts. Under CircuitBreaker, permissions are managed independently per contract, so emergency response capability is preserved.
Source: Lido
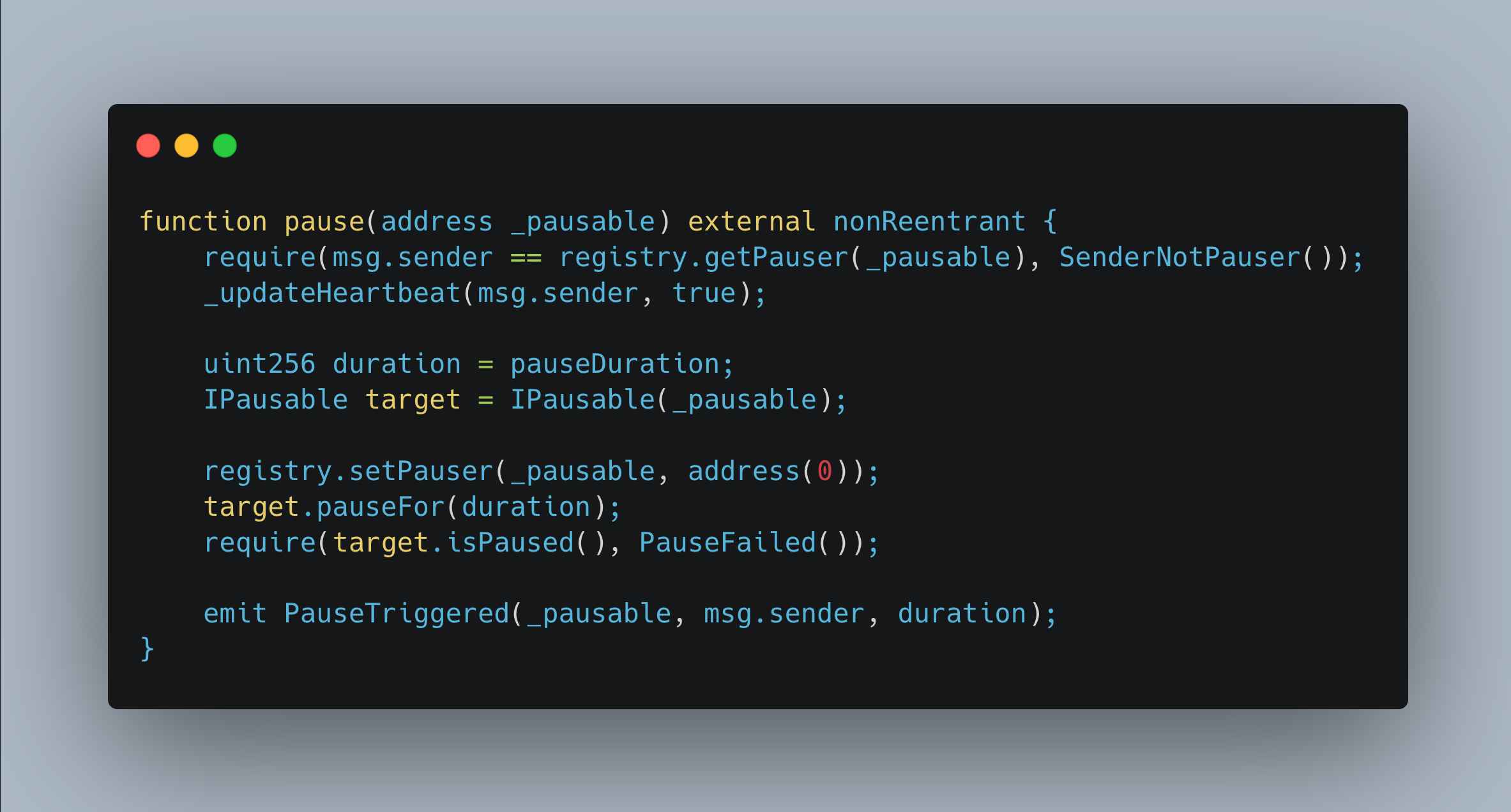
The third, and the most noteworthy design element, is the heartbeat (proof of liveness). The committee must periodically send heartbeat transactions to prove on-chain that it is ready to respond in an emergency. A committee whose heartbeat has expired can neither trigger a pause nor renew its heartbeat; the DAO must replace it with a new committee. Where GateSeal used contract expiration to draw the DAO's attention, CircuitBreaker uses committee liveness expiration to serve the same function, but through a single lightweight transaction rather than a heavyweight redeployment process.
Source: Lido
In fact, during a GateSeal drill conducted in June 2024, the full committee was assembled and completed a simulated trigger in 25 minutes. The heartbeat can be seen as taking the idea of verifying committee liveness, which was tested during the 2024 drill, and evolving it into a mechanism that is enforced periodically on-chain.
Among the parameters proposed for CircuitBreaker, the most important is the pause duration. GateSeal had pause durations of initially 6 days, then 11 days, but CircuitBreaker proposes an initial value of 21 days. This number comes from the following arithmetic.
After an emergency pause is triggered, the DAO must hold a vote on follow-up measures. An Aragon vote takes 5 days, and if quorum is not met, a revote adds another 5 days. Under Dual Governance, an additional timelock of at least 4 days is required for stETH holders to exercise their veto rights. That totals 14 days, and adding a 7-day buffer for situation analysis, development team coordination, and vote preparation brings it to 21 days.
Dual Governance has a significant impact on this calculation. Previously, the DAO could take follow-up action with a single vote after an emergency pause. But with Dual Governance, an additional window has been introduced for stETH holders to challenge the decision. In other words, the entire governance process has lengthened, so the pause duration must extend accordingly. If the pause expires before the governance cycle completes, the worst-case scenario occurs: a contract resumes while the vulnerability remains unpatched.
Source: Lido
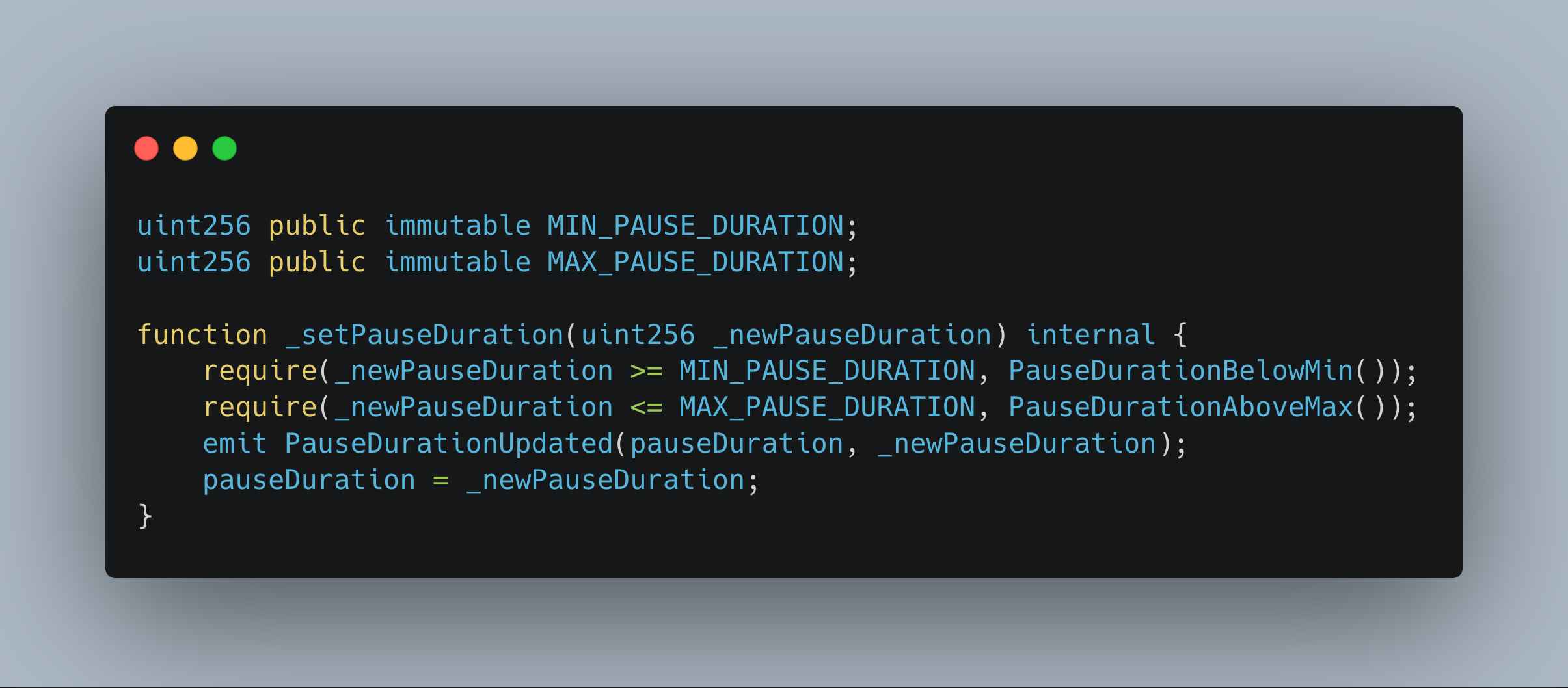
The immutable boundary values are also worth noting. Lido hardcodes a floor of 5 days and a ceiling of 60 days for the pause duration directly in the contract. The DAO can adjust the initial value of 21 days using its admin privileges, but it cannot exceed these boundaries. This is a safeguard that prevents abuse of the protocol even if the DAO itself falls victim to a governance attack, by making it impossible to shrink or stretch the pause duration to extreme values.
On the other hand, the fact that CircuitBreaker is implemented as a single contract raises the possibility that a vulnerability could disable the entire emergency pause capability. Lido addresses this by minimizing the attack surface through a structure that uses only a single, self-contained library with no external dependencies. Additionally, under Dual Governance, the Reseal Committee can extend CircuitBreaker's initial pause if necessary, providing a secondary layer of defense.
The core value of CircuitBreaker lies not in the emergency pause function itself, but in structurally lowering the cost of maintaining that function. CircuitBreaker preserves what GateSeal solved, namely emergency response faster than governance, while eliminating the problem GateSeal created: the operational debt of periodic redeployment.
That said, the heartbeat model introduces a subtle tradeoff. GateSeal's forced expiration served as a natural coordination point. As the expiration date approached, the entire DAO became aware that "our emergency pause capability is about to disappear," prompting public discussion and collective action. When renewal proposals went up, they sparked forum discussions and gave the community an occasion to review the current security posture. With CircuitBreaker, heartbeat expiration risks becoming an internal committee matter, potentially weakening the attention-raising effect across the broader DAO. This can be supplemented with monitoring and alerting systems, but there is a difference in reliability between structural enforcement and operational monitoring.
Source: Lido
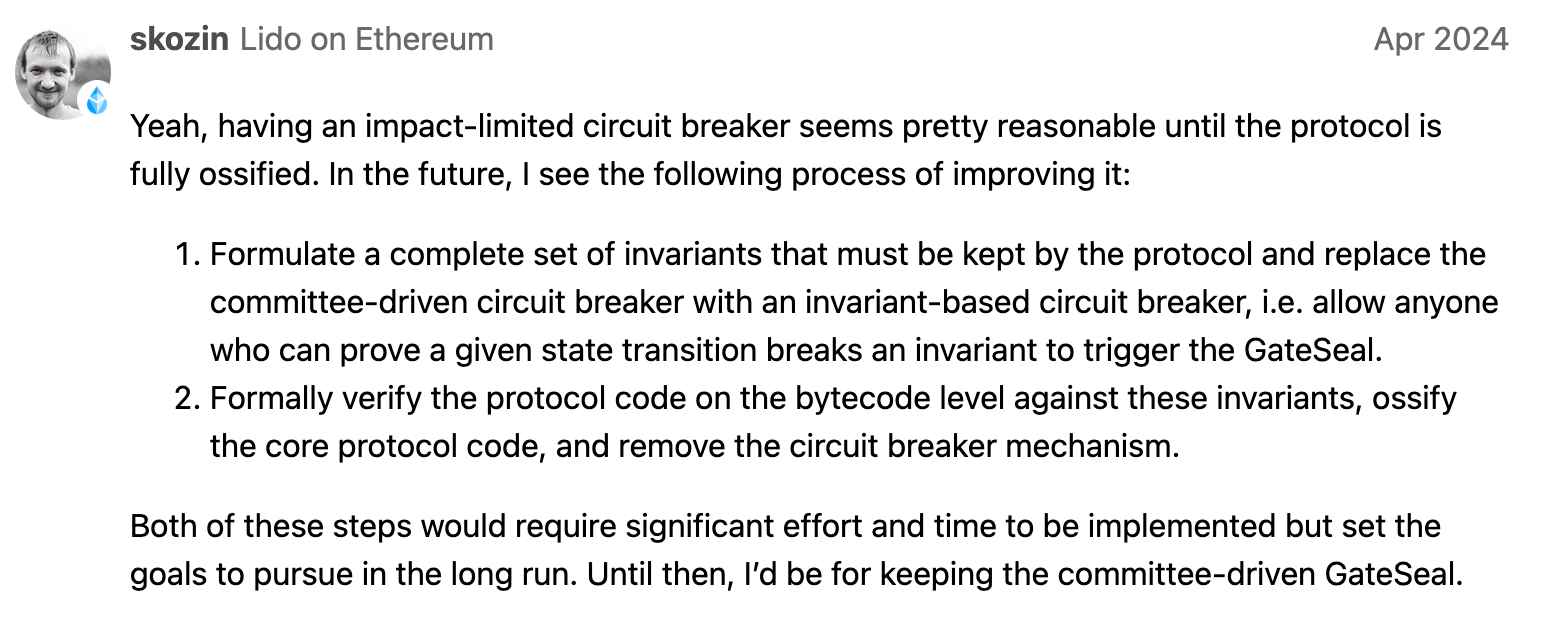
Regarding the long-term direction for emergency pause mechanisms, a comment left by Lido developer skozin during the April 2024 GateSeal renewal discussion is worth referencing. He proposed a transition toward a permissionless circuit breaker, where the protocol's invariants would be formalized so that anyone could submit a proof that "this state transition violates an invariant," automatically triggering a pause. The ultimate endpoint, he suggested, would be eliminating the circuit breaker altogether through formal verification of protocol code and ossification of core logic.
This provides a useful frame for situating where CircuitBreaker stands. CircuitBreaker does not remove the trust assumption of a committee right away, but by reducing the governance resources previously consumed by annual renewals, it can free up space to explore these next steps.
The fundamental question that the CircuitBreaker proposal raises is: "How long can a decentralized protocol justify relying on a centralized tool like emergency pausing?" If CircuitBreaker is successfully adopted, it could serve as a reference case in governance design for gradually reducing trust assumptions, not only for Lido but also for other DeFi protocols facing a similar dilemma.
Dive into 'Narratives' that will be important in the next year