Much like in January and February, March’s proposals reflect a growing set of complex challenges emerging alongside the protocol’s maturation, and, as a result, Core EIP discussions are not only expanding in scope but also unfolding in increasingly granular and specialized directions.
Looking ahead to the second half of the year, following the Hegota Upgrade, the introduction of FOCIL is expected to expose the structural limitations of the current builder–relay-centric paradigm; in turn, this will likely catalyze more active discussions around follow-up proposals, including enshrined PBS, encrypted mempools, and fee market design.
Meanwhile, in March, Ethereum Foundation revisited Ethereum’s identity and role through two blog posts. Anchored in unforkable persona grounded in the CROPS principles, and reinforced by years of accumulated trust and ecosystem maturity, Ethereum is poised to further evolve into a more robust form of public infrastructure.
Ethereum pioneered the concept of smart contracts by integrating programmability into a distributed ledger architecture, thereby expanding the functional scope of blockchain systems. This design philosophy has been progressively formalized through the Ethereum Improvement Proposal (EIP) process, enabling the network to evolve beyond a simple store of value into an infrastructure capable of supporting real-world businesses and a wide range of use cases. As this evolutionary process continues, broader participation in EIP deliberations—by opinion leaders with heterogeneous perspectives and problem framings—may further enrich the development of a digital-native economic paradigm.
This article presents a high-level examination of EIP trends by reviewing proposals newly accepted into the Draft stage on a monthly basis, alongside proposals that have undergone meaningful status transitions. Through this analysis, we aim to provide builders and business stakeholders with a more structured understanding of the evolving EIP landscape and to offer a conceptual foundation for identifying and developing new value propositions within their respective areas of activity.
The EIP-related data referenced in this article was collected and analyzed using the official GitHub repositories for EIP, ERC, and RIP.
One of the most notable characteristics of March’s EIP landscape is the continued emergence—following January and February—of a meaningful number of new proposals at the Core category, introduced both consistently and across a wide range of domains. This trend suggests that, as the protocol matures, the number of problems that must be addressed simultaneously is increasing, and, in response, the EIP pipeline itself is becoming more parallelized in nature.
More specifically, as demand continues to rise across data availability and gas optimization, more flexible transaction types and execution models, as well as cryptography-driven solutions and quantum-resistant mechanisms—spanning scalability, UX, and overall L1 security—protocol-level discussions are becoming increasingly active. Within this context, there is a clear shift toward breaking down functionalities into smaller, modular components that can be more rapidly integrated into the protocol, with EIP design itself becoming progressively more granular.
At the application layer, ERC standards—arguably a reflection of broader industry trends—have also seen meaningful progress. As will be explored in later sections, standards spanning on-chain membership representation, cross-chain messaging, and more expressive royalty frameworks (capable of both defining relationships with greater precision and controlling their propagation scope) have advanced significantly; notably, of the six major EIP developments in this category, five have already reached the “Final” stage, underscoring the accelerating pace of standardization at the application layer.
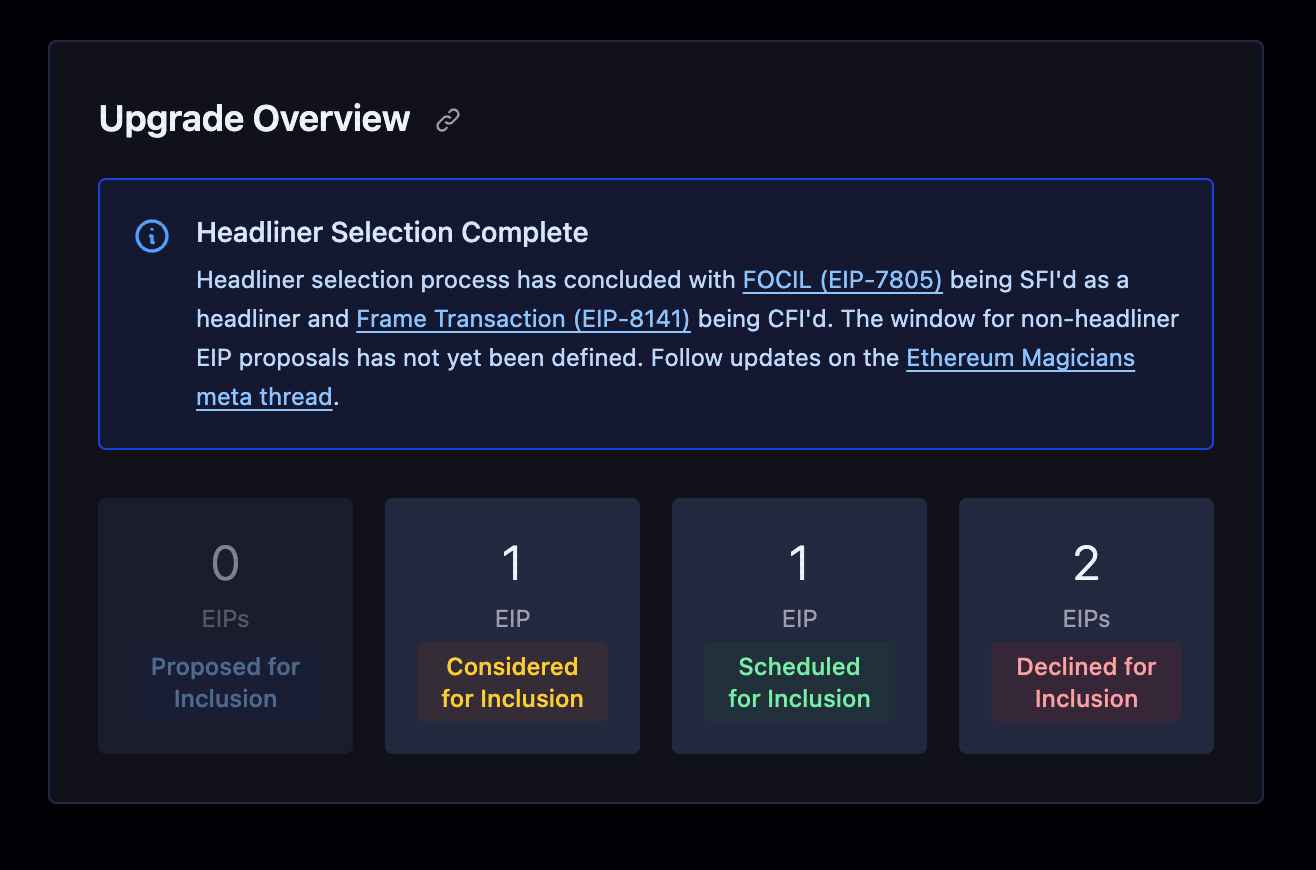
Source: forkcast
Meanwhile, within the Ethereum community, discussions around the selection of headliners for the next upgrade, Hegota Upgrade, continued actively throughout the month, extending the momentum from February. On the consensus layer (CL) side, FOCIL (Fork-choice Enforced Inclusion Lists, EIP-7805)* has been designated as SFI (Scheduled for Inclusion), while on the execution layer (EL), Frame Transactions (EIP-8141)** have been elevated to CFI (Considered for Inclusion), placing them under continued review. Beyond these two proposals, discussions remain ongoing regarding which additional EIPs are suitable for inclusion in the Hegota upgrade.
Taking these developments together, it becomes increasingly likely that, in the post-Hegota landscape, the introduction of FOCIL will mark a structural shift whereby transaction inclusion is no longer a discretionary choice but a protocol-enforced rule. As a consequence, the existing block production paradigm—largely centered around builders and relays—is expected to reveal its structural limitations, naturally amplifying the need for subsequent initiatives aimed at re-aligning inclusion and ordering at the protocol level. This includes efforts such as enshrined PBS (EIP-7732), encrypted mempools (EIP-8184), and fee market redesigns, all of which are likely to become focal points of increasingly active discussion.
*FOCIL proposes a protocol-level rule designed to prevent block builders from arbitrarily excluding transactions; specifically, it introduces a mechanism whereby a validator committee defines a list of transactions that must be included, and enforces their inclusion at the block level. In doing so, it is widely regarded as a meaningful step toward reinforcing Ethereum’s core principles(i.e., censorship resistance and credible neutrality) directly at the protocol layer.
**Frame Transactions, on the other hand, remain under active debate, with proponents highlighting their potential benefits while critics continue to raise concerns around implementation complexity. For a more detailed discussion of the Frame Transactions, please refer to the separate article by Four Pillars researcher r2jamong.
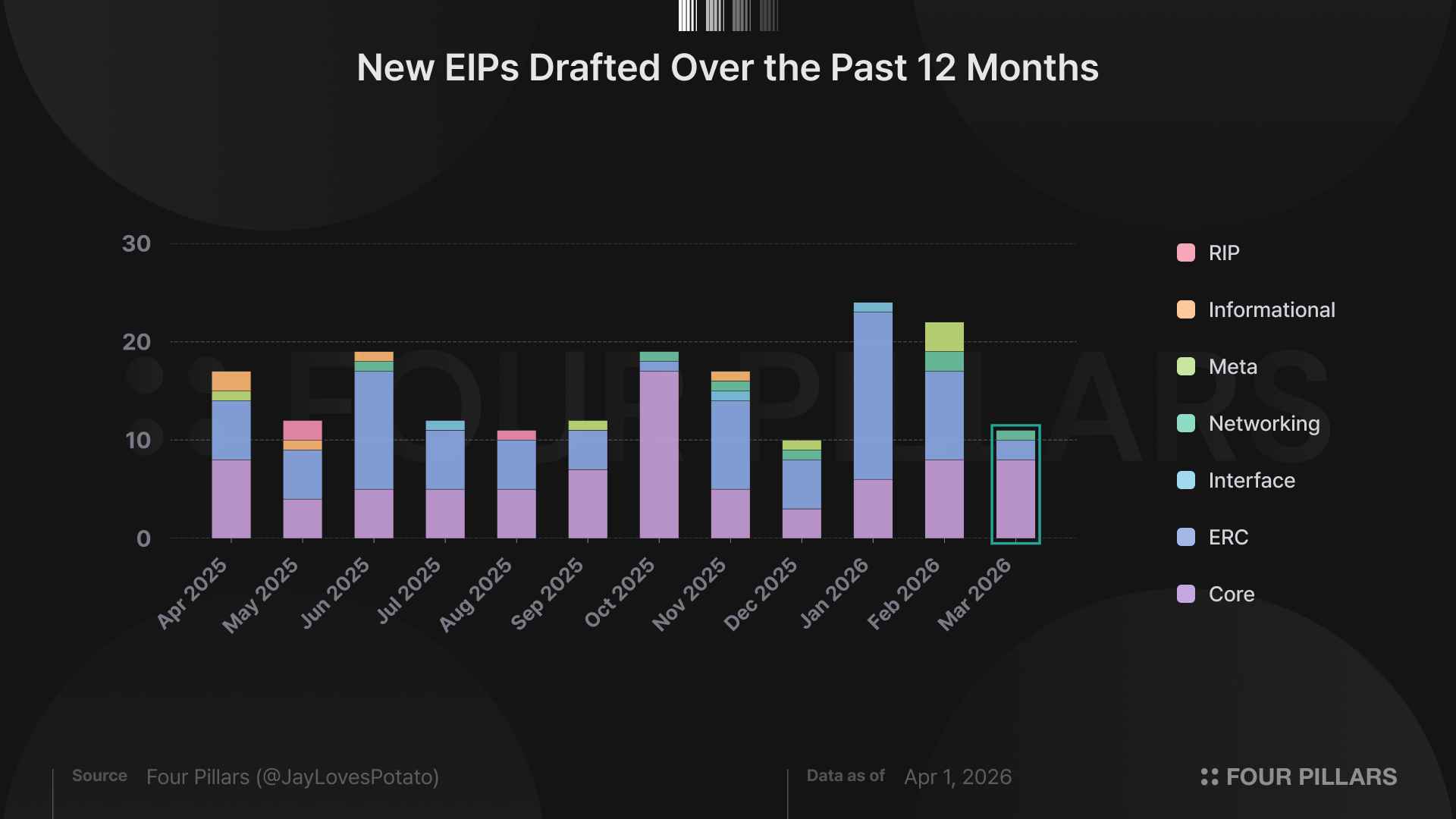
In March, a total of 11 EIPs were newly adopted into Draft status, representing a decrease of 11 compared to the previous month. The majority of these newly drafted proposals were concentrated in the Core category.
Below, we take a closer look at these newly drafted EIPs by breaking them down into more detailed categories, followed by a deeper examination of several proposals that warrant particular attention.
2.1.1 EIP-8163: Reserve EXTENSION (0xae) opcode
This EIP was previously covered by Four Pillars researcher C4lvin in a separate post; the following is a lightly adapted version of the original write-up.
Proposed by Monad Labs, EIP-8163 introduces the idea of permanently reserving the 0xae opcode within Ethereum L1’s EVM. By doing so, it effectively creates a standardized extension prefix that external EVM-based chains can freely leverage for custom functionality. In essence, by formally committing that “this opcode will never be used” at the L1 level, Ethereum provides a guaranteed namespace—allowing other EVM chains to experiment with extensions without the risk of opcode collisions.
The significance of this proposal lies in its attempt to ease the structural dependency dilemma faced by EVM-based alternative(alt) L1s. Building a fully independent VM entails substantial ecosystem bootstrapping costs, while adhering strictly to the EVM leaves chains exposed to upstream protocol changes on Ethereum L1. As such, these chains are often forced into a trade-off between sovereignty and compatibility.
Recent debates around EIP-8141 (Frame Transactions) illustrate this tension clearly. The proposal introduces a model in which transaction validity is dynamically determined based on execution results within a validation frame; however, for chains like Tempo—with their own transaction design—this effectively results in mandatory integration of unused (and therefore dead) code. For architectures such as Monad, which decouple consensus and execution by agreeing on transaction ordering first and executing them in a separate pipeline, it imposes a “pre-consensus execution requirement” that fundamentally conflicts with their design. In other words, maintaining EVM equivalence necessitates adoption, while rejecting it comes at the cost of compatibility.
Against this backdrop, Monad’s EIP proposal of EIP-8163 reads as a natural progression. Rather than remaining passively coupled to L1 protocol changes, it seeks to establish a bounded extension space within which individual chains can experiment in alignment with their own architectural preferences—without fragmenting the broader EVM ecosystem.
Importantly, the proposal introduces no effective protocol changes to Ethereum L1 itself, and any successful extensions can later be upstreamed via separate EIPs. Given that the pace of Ethereum’s evolution is ultimately constrained by the complexity that client developers and tooling providers can reasonably absorb, EIP-8163 offers a pragmatic workaround—enabling parallel experimentation without overburdening the core protocol.
*On Ethereum L1, the opcode behaves identically to INVALID (0xfe), meaning it introduces no native protocol-level changes or risks.
2.1.2 EIP-8184: LUCID encrypted mempool
EIP-8184 begins with a reframing of the MEV problem on Ethereum—not merely as a byproduct of market structure, but as a structural limitation rooted in the transparency of the public mempool itself.
In the current design, transactions are exposed the moment they are propagated, inherently granting searchers and builders an asymmetric informational advantage. As a result, users remain persistently vulnerable to adverse price execution, sandwich attacks, and even forms of censorship.
To address this, EIP-8184 proposes implementing an encrypted mempool at the protocol level, where transactions remain encrypted throughout their lifecycle until inclusion.
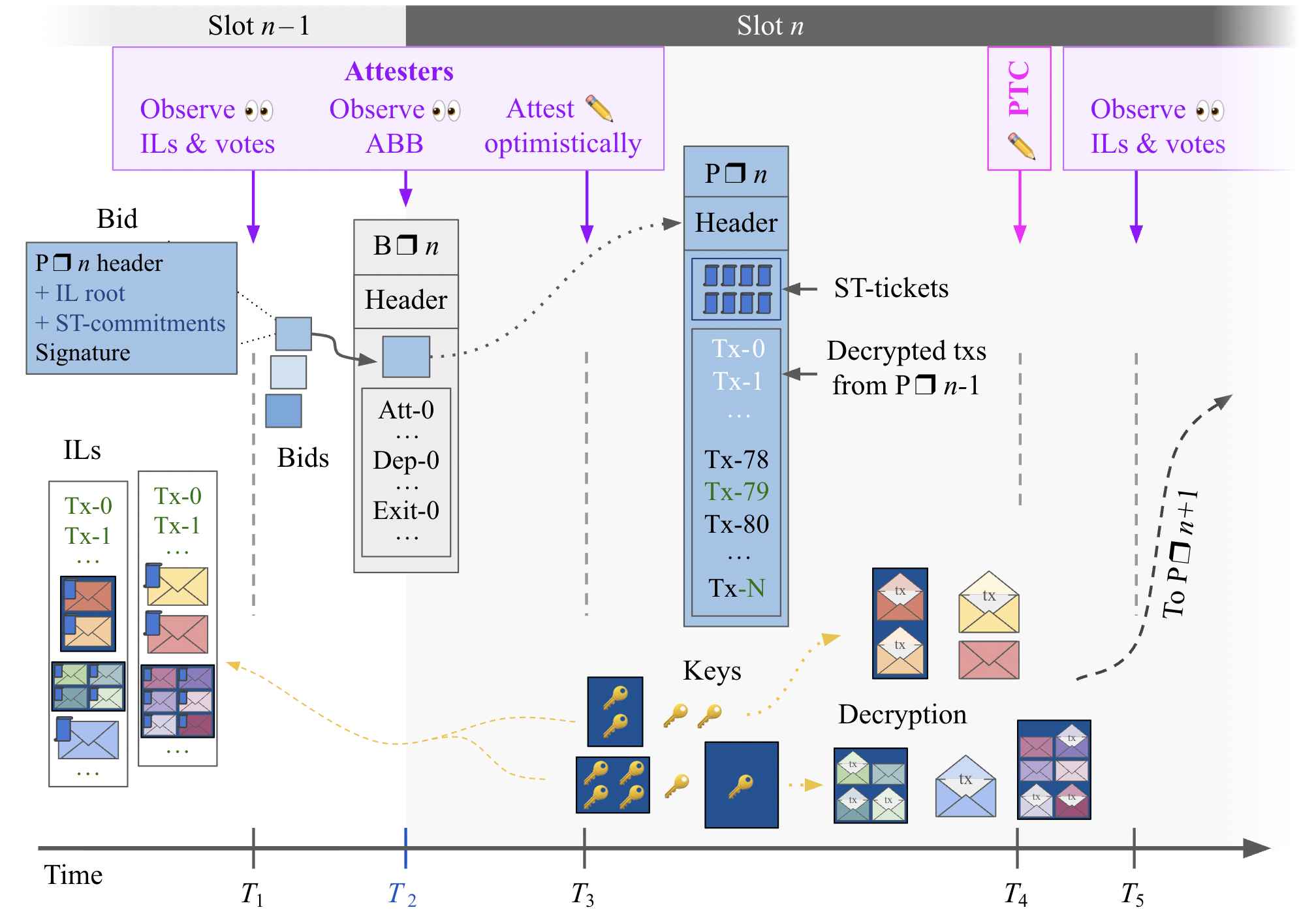
Source: EIP-8184
Concretely, transactions are submitted not as plaintext, but as encrypted payloads composed of elements such as ciphertext, commitment, and a corresponding decryption key. These encrypted transactions propagate through the network, and builders, unable to interpret their contents, are forced to perform ordering without informational advantage; only after certain conditions are met are the transactions collectively decrypted—by a designated decryptor or key publisher—at which point their execution details are revealed.
Another key aspect of EIP-8184 lies in its design philosophy: rather than attempting to eliminate front-running entirely, it focuses on managing risk in a controlled and parameterized manner. This is exemplified by variables such as max_preceding_commitments, which effectively cap the number of commitments that may precede a given transaction, thereby bounding ordering uncertainty within a predictable range. In other words, users trade away absolute ordering guarantees in favor of a system where competition is permitted—but only within explicitly defined limits. This reflects a pragmatic compromise, one that preserves network flexibility while meaningfully constraining excessive MEV extraction*.
If adopted, and if encrypted mempools become enshrined at the protocol level, the role of block builders would likely undergo a fundamental shift—from strategic actors optimizing based on informational asymmetry to more neutral participants responsible primarily for ordering and inclusion. In interaction with PBS (Proposer-Builder Separation) structure, this could reshape the competitive dynamics of the builder market altogether.
At the same time, this design introduces new classes of risk, including potential delays or failures in the decryption process, as well as challenges around key management. These factors may necessitate a reconfiguration of Ethereum’s underlying trust model. Nevertheless, EIP-8184 represents a meaningful attempt to transition from a market structure defined by informational asymmetry to one grounded in cryptographic fairness—positioning it as a proposal with potentially far-reaching implications for Ethereum’s long-term market design.
*This contrast becomes even clearer when compared to EIP-8105. While both proposals share the goal of enabling encrypted mempools, EIP-8105 takes a more rigid approach, relying on a trust graph among key publishers to structurally prevent untrusted actors from preceding a given transaction—effectively eliminating front-running at the ordering layer itself. EIP-8184, by contrast, opts for a more flexible model: rather than imposing strict trust constraints, it allows bounded competition through parameterization. Notably, the EIP-8105 team has expressed full support for the EIP-8184 initiative, signaling a convergence of design direction despite differing underlying philosophies.
2.1.3 EIP-8189: snap/2 - BAL-Based State Healing
EIP-8189 proposes a structural redesign of the “healing stage” in Ethereum’s state synchronization (snap sync) process. The existing approach relies on repeatedly requesting individual Merkle trie nodes to fill in missing state, resulting in high network round-trip costs and added implementation complexity.
Instead, EIP-8189 replaces this model by reconstructing state using the Block Access List (BAL, EIP-7928), a block-level aggregation of state changes, offering a more efficient and streamlined synchronization mechanism.
More concretely, the following message-level changes are introduced:
Removed:
GetTrieNodes (0x06)
TrieNodes (0x07)
Added:
GetBlockAccessLists (0x08)
BlockAccessLists (0x09)
In other words, whereas the previous approach required exploratory requests for trie nodes without knowing exactly which state was missing, this proposal enables clients to fetch BALs for a given block range and reconstruct the state deterministically through sequential application*.
This proposal carries meaningful implications for Ethereum’s scalability and client-side implementation complexity. The existing trie-based healing stage is network-intensive, highly sensitive to latency and bandwidth, and introduces considerable implementation overhead for clients. In contrast, a BAL-based approach linearizes the data flow and allows the required scope of information for synchronization to be determined in advance. This can represent a particularly significant improvement for light clients and fast node bootstrapping scenarios.
That said, as the proposal itself acknowledges, the increased size of BAL data and the need to reliably propagate it across the network introduce new overhead that must be carefully considered. Nevertheless, EIP-8189 illustrates Ethereum’s broader shift toward a more modular and data-efficient architecture, and lays the groundwork for future extensions such as state-diff-based synchronization or partial state provisioning models.
*At its core, the BAL mechanism commits block-level state changes as a structured dataset, with each block including a block-access-list-hash in its header. As a result, a syncing node need only download the corresponding BAL data and verify its consistency against the block header.
2.1.4 EIP-8198: Quick Slots
EIP-8198 begins with the observation that Ethereum’s relatively long latency is not merely a UX inconvenience, but a structural constraint that affects the broader market. At present, Ethereum produces blocks based on a fixed 12-second slot time—an arbitrary constant that has increasingly become a bottleneck in both user experience and market efficiency. The longer the slot duration, the more delayed transaction finality becomes, exacerbating DEX price divergence, arbitrage losses, and opportunities for MEV extraction. Moreover, extended block intervals grant builders greater optionality—allowing them to make more informed, and often more extractive, decisions—which in turn contributes to inefficiencies such as empty blocks and broader market distortions.
To address this, EIP-8198 adopts a staged and adaptive approach. At its core, the proposal replaces SLOT_DURATION_MS as a compile-time constant with a runtime parameter, thereby enabling the protocol to dynamically determine and adjust the optimal slot duration over time*.
What is particularly notable, however, is that this proposal does not aim to increase absolute throughput. Instead, as slot durations shorten, parameters such as the block gas limit and blob-related capacities are proportionally adjusted to maintain a consistent throughput per unit of time. In other words, rather than simply “making blocks smaller,” the design carefully rescales resource units in alignment with reduced time intervals—achieving a precise trade-off where latency is selectively reduced without increasing overall network load.
The implications of this extend well beyond surface-level UX improvements. A reduction in L1 latency naturally propagates to faster L2 sequencing, thereby enhancing responsiveness across rollup ecosystems. At the same time, it has the potential to compress MEV opportunities, improve price alignment across markets, and reduce reliance on off-chain mitigation mechanisms such as preconfirmation.
That said, shortening slot durations introduces new challenges, including stricter requirements on network propagation, client performance, and validator operations. Furthermore, because this change fundamentally alters consensus-layer behavior, its initial implementation would necessarily require a hard fork. Nevertheless, the proposal lays the groundwork for a more flexible block time architecture—one that, even if immediate performance gains are incremental, opens the door to more sophisticated client designs and deeper exploration of consensus-layer performance dynamics.
*Looking ahead, discussions are already exploring the possibility of enabling gradual performance tuning through parameter adjustments without requiring additional hard forks—for instance, by varying slot durations at the epoch level or adapting time parameters dynamically based on real-time network conditions.
2.1.5 Others
2.2.1 EIP-8182: Private ETH and ERC-20 Transfers
At its core, EIP-8182 proposes introducing a natively embedded privacy transfer mechanism into Ethereum. Under the current design, all transactions executed at the protocol level are fully transparent, which makes use cases such as payroll distribution or corporate treasury movements inherently exposed. As a result, privacy solutions have historically emerged at the application layer in a fragmented manner—leading to weakened anonymity sets and fragmented liquidity. EIP-8182 addresses this by proposing a shared, protocol-level privacy pool, designed to aggregate users into a single, unified anonymity set.
Technically, the proposal is centered around a Two-Circuit Architecture, which separates responsibilities between an outer circuit and an inner circuit. The outer circuit enforces critical invariants—such as balance conservation, nullifier checks (to prevent double-spending), and Merkle proof verification—ensuring that the system’s core integrity remains uncompromised. The inner circuit, by contrast, governs authentication logic (e.g., ECDSA, passkeys, multisig), and is designed to be extensible. This separation allows new authentication schemes to be introduced without requiring protocol-wide upgrades—preserving security guarantees while significantly enhancing flexibility.
In practice, the proposed EIP operates in a relatively intuitive manner: users deposit funds into the privacy pool, transact privately within it, and withdraw when needed. Throughout this lifecycle, system contracts manage key components such as the commitment tree, nullifier set, user registry, and authentication policy registry, while verifying proofs and updating state on a per-transaction basis. Notably, through functions like registerAuthPolicy, users can register multiple authentication schemes, enabling a single address to flexibly support diverse authorization models.

Source: EIP-8182
What makes this proposal particularly compelling is that it goes beyond simple anonymity, instead introducing what can be described as a “hybrid privacy layer” in a flexible manner. While transactions are concealed by default, the system supports optional origin-tagged notes, allowing users to selectively prove the provenance of funds when required. This creates a flexible middle ground between full anonymity and full transparency—one in which compliance layers can be selectively overlaid, making the system compatible with AML requirements, accounting standards, and broader institutional constraints.
That said, the proposal comes with meaningful constraints. The system contracts are non-upgradeable, meaning that any flaws in the privacy design would be difficult to rectify without a hard fork. Additionally, the scope of the EIP explicitly excludes mempool-level privacy and network-layer anonymity, limiting its coverage to execution-layer privacy only.
Nevertheless, EIP-8182 represents a significant step forward in Ethereum’s evolution—not just as a shared settlement layer, but as a network capable of supporting both shared settlement and shared privacy.
2.2.2 Others
2.3.1 ERC-8167: Modular Dispatch Proxies
ERC-8167 proposes a standardized modular dispatch proxy architecture, designed to address the limitations of traditional monolithic proxy patterns. Instead of delegating all logic to a single implementation contract, this approach introduces function selector–based routing, enabling logic to be split across multiple delegate modules and dynamically dispatched at runtime.
In conventional proxy designs, all functionality is tied to a single implementation, meaning upgrades often require replacing the entire contract—introducing both operational friction and systemic risk. ERC-8167, by contrast, decomposes logic at the function level, executing delegatecall based on individual selectors. This allows developers to selectively upgrade or extend specific functionalities without affecting the entire system, while also bypassing code size limitations and structurally enhancing shared logic reuse and composability.
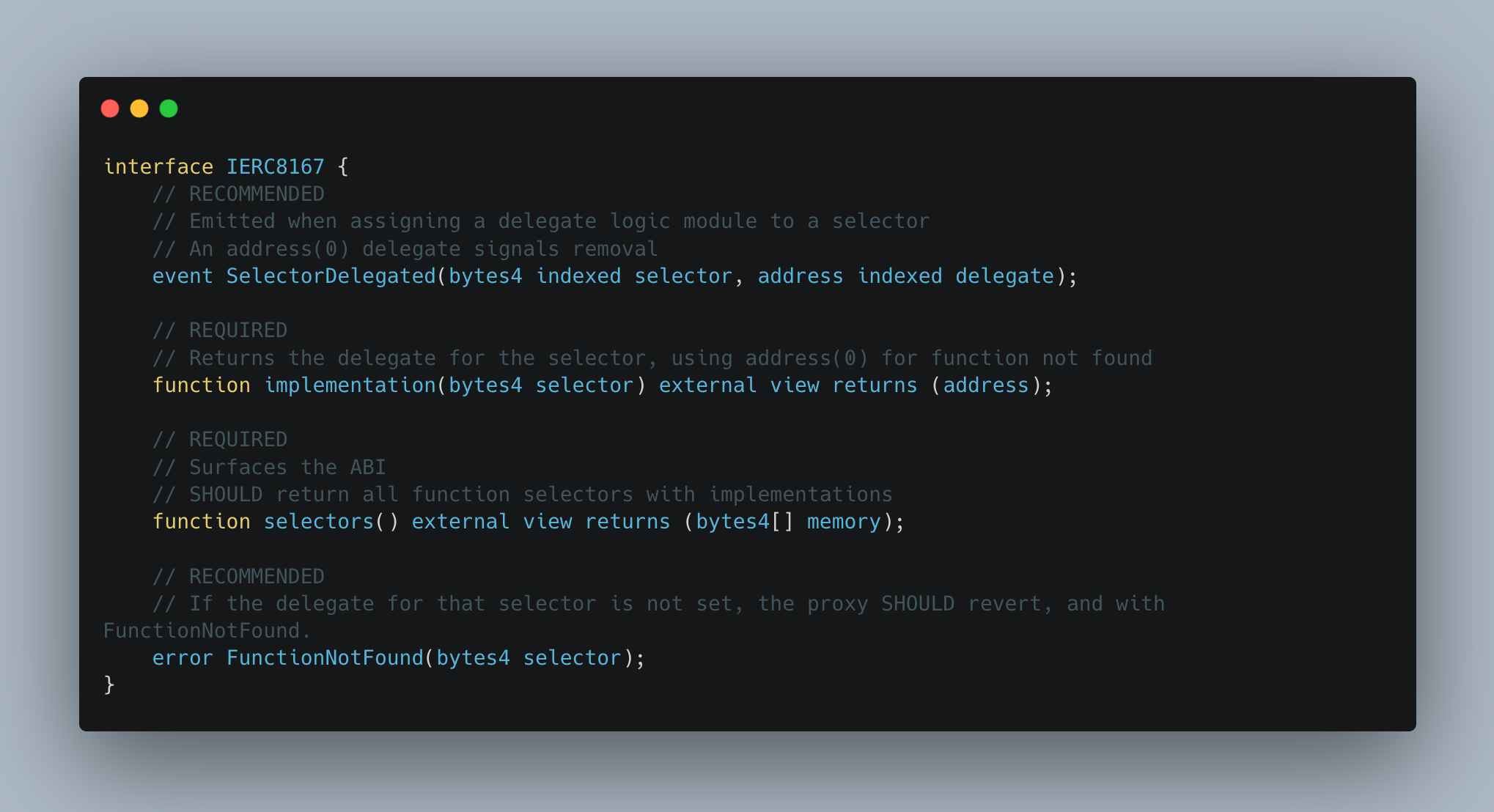
Source: ERC-8167
Looking more closely at the code, the core idea of ERC-8167 is to map delegates based on the first 4 bytes of calldata (the selector), retrieve the corresponding delegate address, and forward the same calldata for execution. In this model, the proxy does not reconstruct or interpret logic—it simply acts as a router, with actual functionality distributed across individual delegate modules.
The implementation(bytes4) function returns which delegate a given selector points to, while selectors() exposes the full list of selectors supported by the proxy. This allows indexers or explorers to collect the selector set and match each one with the corresponding delegate’s ABI, effectively reconstructing the full interface of the proxy. If no delegate exists for a given selector, it is recommended to revert with a FunctionNotFound error.
Consequently, ERC-8167 is significant in that it shifts the upgrade paradigm of smart contracts from wholesale batch replacement to incremental evolution. Whereas previously a single change could introduce system-wide risk, this model enables gradual, module-level updates. It also allows new standards or features to be introduced by simply adding new modules rather than replacing existing contracts. This provides critical flexibility in rapidly evolving domains such as account abstraction, smart accounts, and token extensions.
However, this architecture also introduces new layers of complexity and security risk. As noted in the EIP’s Security Considerations section, a delegatecall-based structure can lead to storage layout collisions, access control vulnerabilities, and severe privilege escalation if delegates are incorrectly registered. Additionally, as logic becomes fragmented at the selector level, overall system traceability and auditability become more challenging.
Despite these trade-offs, the minimal standard interface proposed by ERC-8167 helps contain this complexity while unifying diverse proxy-based modular designs under a common framework. In doing so, it paves the way for Ethereum smart contracts to evolve from monolithic structures into modular execution layers.
2.4.1 ERC-8183: Agentic Commerce
This EIP was previously covered by Four Pillars researcher Jun in a separate post; the following is a summarized and lightly adapted version of the original write-up.
Transactions fundamentally rely on trust between counterparties. However, in on-chain environments, such trust is difficult to assume, which structurally limits the scope of commerce. In response, the Ethereum Foundation’s dAI team, together with Virtuals Protocol, proposed ERC-8183 as a new standard for agentic commerce—aimed at enabling broader use cases, particularly in the context of increasingly prevalent agent-based workflows.
On-chain today lacks a mechanism to reliably assess and enforce individual creditworthiness, which constrains commerce to inherently limited forms. Past attempts, such as Spectral Protocol, sought to introduce on-chain credit scoring models but failed to sustain market adoption. This reflects not merely a lack of data, but the absence of key prerequisites for credit systems—enforceability, identity, and continuity—which are difficult to establish on-chain.
Against this backdrop, ERC-8183 takes a different approach. Rather than attempting to precisely estimate trust between agents, it redesigns the transaction structure itself to support agent-to-agent interactions. In doing so, it does not eliminate trust, but instead repositions it structurally—mitigating counterparty risk while laying the groundwork for a fundamentally new model of how on-chain commerce can operate.
Source : ERC-8183
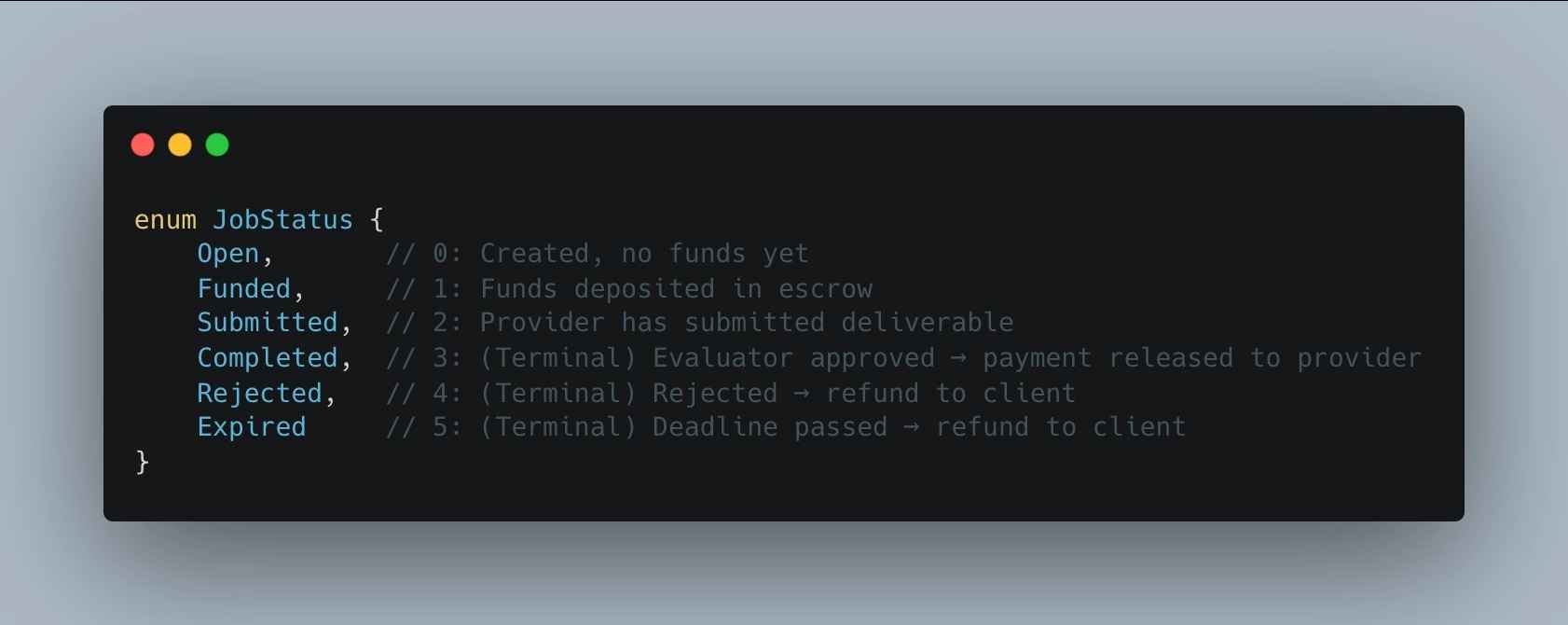
The proposal defines four core components for agent-to-agent commerce: Job, Escrow, Evaluator, and Hook. Every transaction is expressed as a Job, and the client must deposit the budget into escrow before the task begins. The state transitions follow Open → Funded → Submitted → Completed/Rejected/Expired, and because funds are pre-locked at the Funded stage, uncertainty around whether payment will be received is effectively eliminated. In this sense, execution of the transaction is structurally guaranteed.
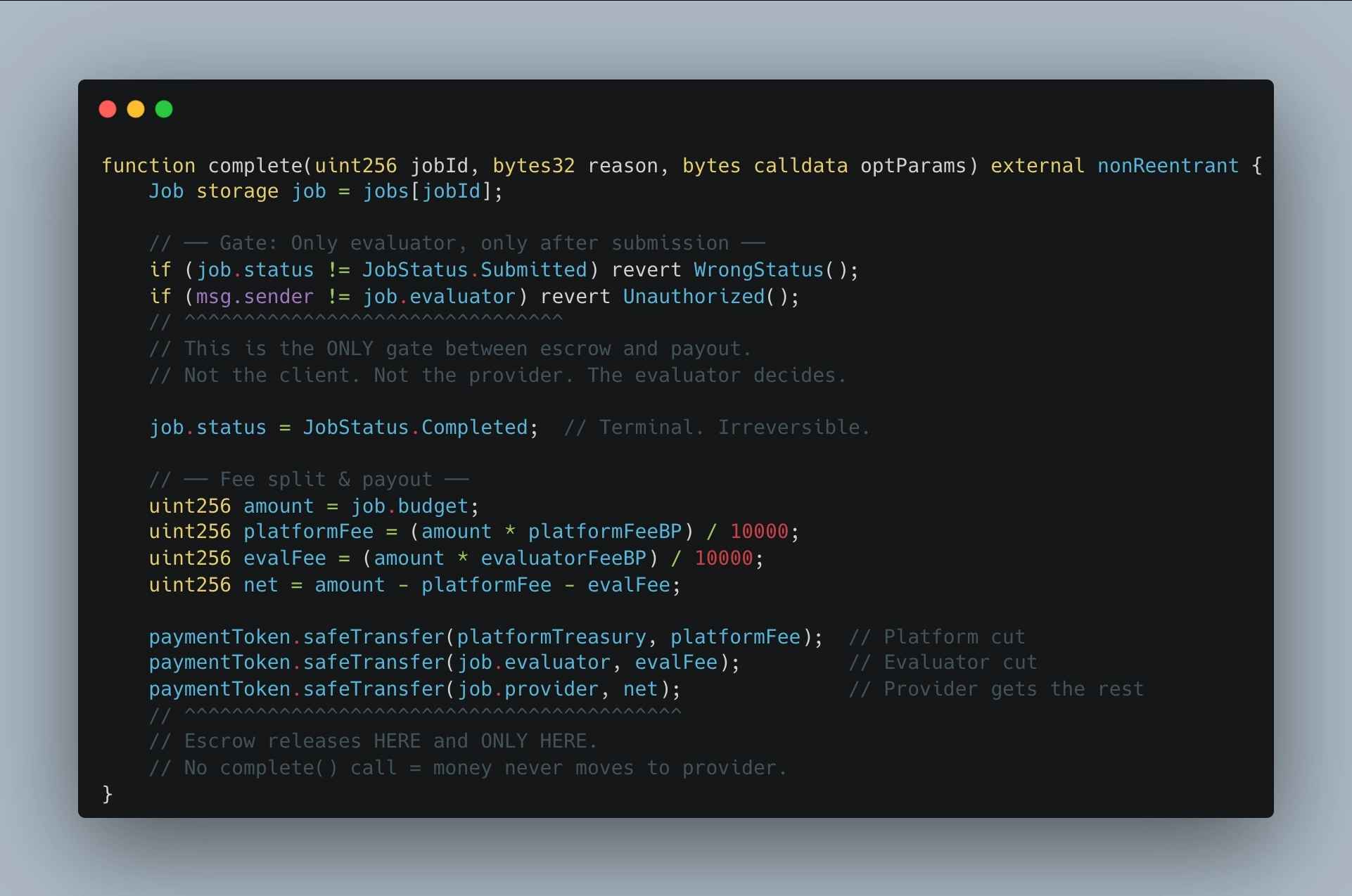
Source : ERC-8183
However, the quality and validity of the output still require evaluation, which is handled by the Evaluator. After submission, only the Evaluator can determine whether a Job is completed or rejected. This suggests that trust is not fully removed, but rather relocated to a specific point in the system. While trust between counterparties is eliminated, decision-making authority becomes concentrated in the Evaluator. To mitigate this, the proposal introduces Hooks and leaves room for integration with external reputation systems—for example, leveraging ERC-8004 to track an Evaluator’s history and credibility.
That said, the risk of malicious behavior by Evaluators still remains, and the proposal does not include protocol-level dispute resolution or enforcement mechanisms. Nonetheless, the significance of ERC-8183 lies not in achieving trustlessness, but in minimizing and localizing where trust is required. By enforcing execution through escrow, enabling selection based on evaluator reputation, and aligning incentives so that honest behavior becomes the rational choice, it presents a more efficient new trust model tailored to on-chain environments.
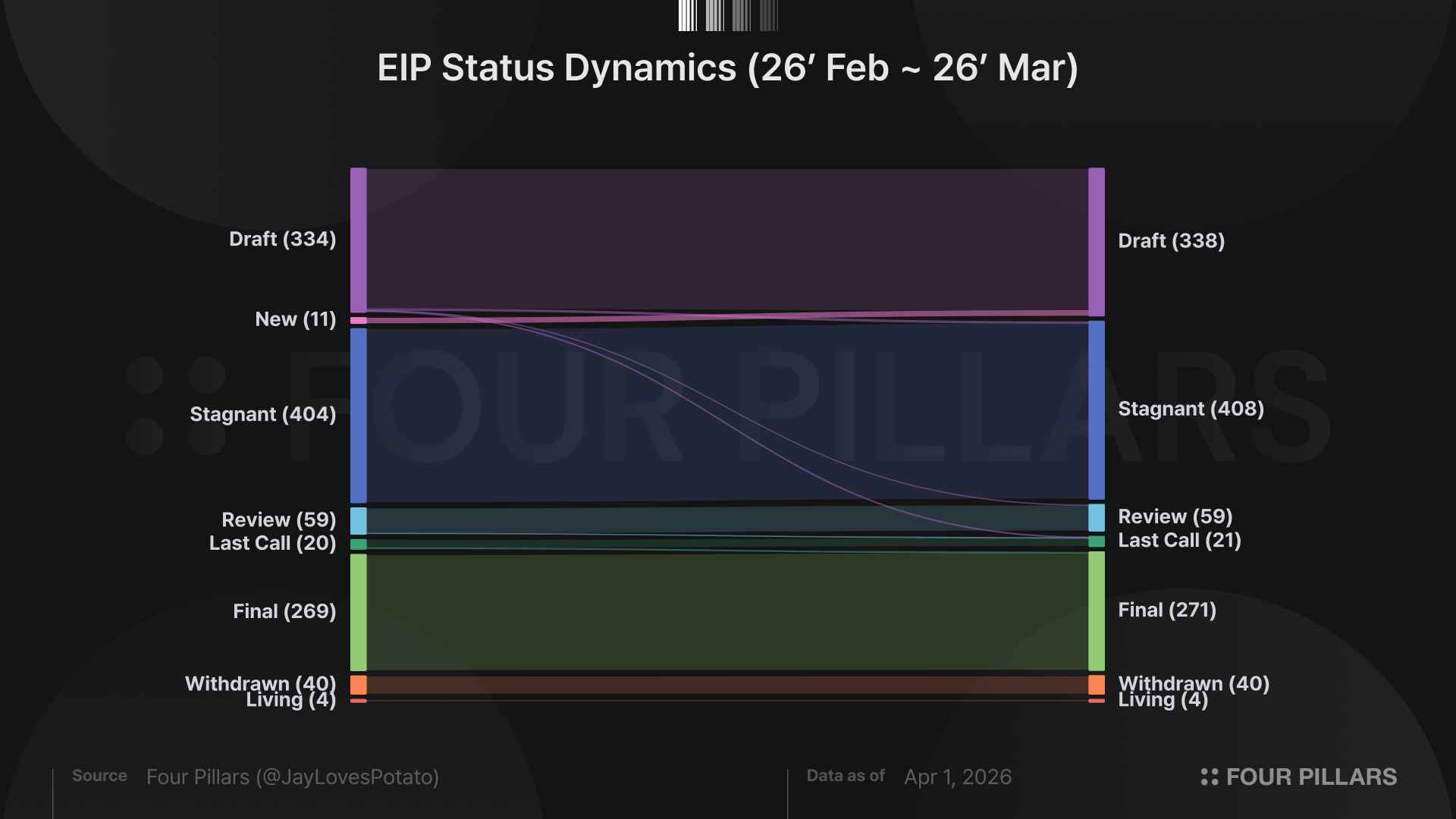
Meanwhile, excluding the 11 EIPs newly adopted into Draft status, a total of 10 existing EIPs experienced status changes during March. Among them, 6 proposals were promoted to the next stage in the standardization pipeline, with 5 in particular reaching the Final stage. The remaining 4 EIPs did not progress and were instead moved to Stagnant status (i.e., EIP-7768, EIP-7792, EIP-7898, and EIP-8013).
Notably, all 6 EIPs that saw progress this month were ERCs implemented at the application layer.
Among the ERCs, several are particularly noteworthy. ERC-7786 introduces a Gateway interface that abstracts cross-chain messaging protocols, enabling them to be swapped in a plug-in-like manner. ERC-7832 standardizes permissioning and revenue-sharing relationships among collaborators, making it possible to create co-authored NFT collections. ERC-8034* proposes an extensible royalty framework within an rNFT-based DAG structure, allowing fine-grained control over royalty distribution and propagation across multiple NFTs. Lastly, ERC-8063 reinterprets ERC-20 token balances as “membership levels,” enabling on-chain representation of group membership and associated permissions.
*This proposal was discussed in greater detail in our previous article.
Additional EIPs of interest are listed below.
In March, two important pieces were published that revisited Ethereum’s identity and role. One outlined the mandate of the Ethereum Foundation, while the other examined Ethereum’s positioning within the L1–L2 architecture. Though each approached the topic from a different layer, both ultimately converged on a single question: “on what principles does Ethereum exist as a system.”
Ethereum extended the concept of decentralization pioneered by Bitcoin—a system sustained by permissionless participants through incentive alignment—and opened a new frontier with smart contracts. Yet its path was far from smooth from the beginning. Designing a globally secure and decentralized P2P network inherently imposed constraints on scalability, which in turn led to criticism around limited practicality. This gap gave rise to numerous alternative L1s, and there were periods when Ethereum’s position appeared uncertain.
Despite this, Ethereum today remains the smart contract platform with the deepest liquidity and the most robust developer ecosystem. While network performance has steadily improved through continuous research and iteration, its current position cannot be explained by technical superiority alone. Rather, it is the result of long-term accumulated trust—and the consistency of direction that made such trust possible. In essence, what has sustained Ethereum is not performance, but its foundational philosophy of what it refuses to compromise on.
At this point, Ethereum’s persona becomes clear. As smart contract platforms are inherently open source, functional differentiation alone is insufficient to sustain long-term adoption in a multi-chain environment. Then, what ultimately matters is an unforkable identity. Ethereum has maintained a set of principles—CROPS (Censorship Resistance, Open Source, Privacy, Security)—that remain intact under all circumstances. These are not merely declarative values, but structural constraints embedded across protocol design and governance, and it is precisely this that differentiates Ethereum from other L1s.
The two recently published blog posts further reinforce and well explain this direction. The Ethereum Foundation does not seek to control or grow the network through centralized influence; rather, it plays a role in minimizing its own authority to preserve the network’s independence and decentralization. At the same time, Ethereum does not attempt to solve everything at the L1, but instead focuses on its role as a trust layer by embracing separation and specialization with L2s.
This structure ultimately translates into what can be described as ecosystem maturity. In an environment where infrastructure performance is increasingly commoditized, the competitiveness of smart contract platforms is no longer determined by short-term performance metrics. Instead, it is defined by the long-term accumulation of sustainable synergies: an environment where diverse applications can emerge, a loyal user base, broad participation, and a distinct culture and operational philosophy. Ethereum has already achieved the deepest level of such maturity, and continues to attract new participants who resonate with its underlying persona—reinforcing a powerful flywheel of ecosystem growth.
Ultimately, Ethereum has proven itself through choices grounded in principle. What began with early contributors aligned around a clear philosophy has, over time, accumulated deep layers of trust and culture—forming a robust foundation. And now, while difficult to quantify, Ethereum appears to have moved beyond mere survival, entering a phase where it is solidifying its position as a uniquely dominant infrastructure at an accelerating pace.
Dive into 'Narratives' that will be important in the next year