*This article was written as a wrap-up for "Modular Harmony" Event.
Modular blockchain is an architectural approach that divides a blockchain's core functions into distinct, interoperable layers to improve scalability, flexibility, and customization. The year 2023 saw the introduction of projects that aimed to innovate within each segmented area. In contrast, 2024 is expected to highlight the importance of collaborations between these projects. Given the interdependency of modular blockchain projects, these collaborations will play a crucial role in the industry.
This ongoing effort, with no signs of waning, has involved many people and developers who envision a brighter future for blockchain. This vision motivated our co-hosts, Radius, Four Pillars, Chainlight, and Decipher, to organize a meeting for researchers and developers to discuss collaborative efforts for an improved future. In this event, named "Modular Harmony," we examined the harmony of components, (1) discussing its past evolution, (2) its current interesting developments, and (3) its potential future development.


The concept of modular blockchain, as popularized by Celestia, represents a shift in the design and functionality of blockchain technology. Unlike traditional, monolithic blockchains that perform all tasks—data availability, consensus, execution, and settlement—within a single, inseparable layer, modular blockchains like Celestia adopt a different approach. They separate these fundamental functions into distinct layers, each optimized for specific tasks. This architectural innovation not only enhances scalability and efficiency but also introduces a new level of flexibility and independence for developers. It does this by decoupling the different functionalities of a blockchain into separate layers or modules.
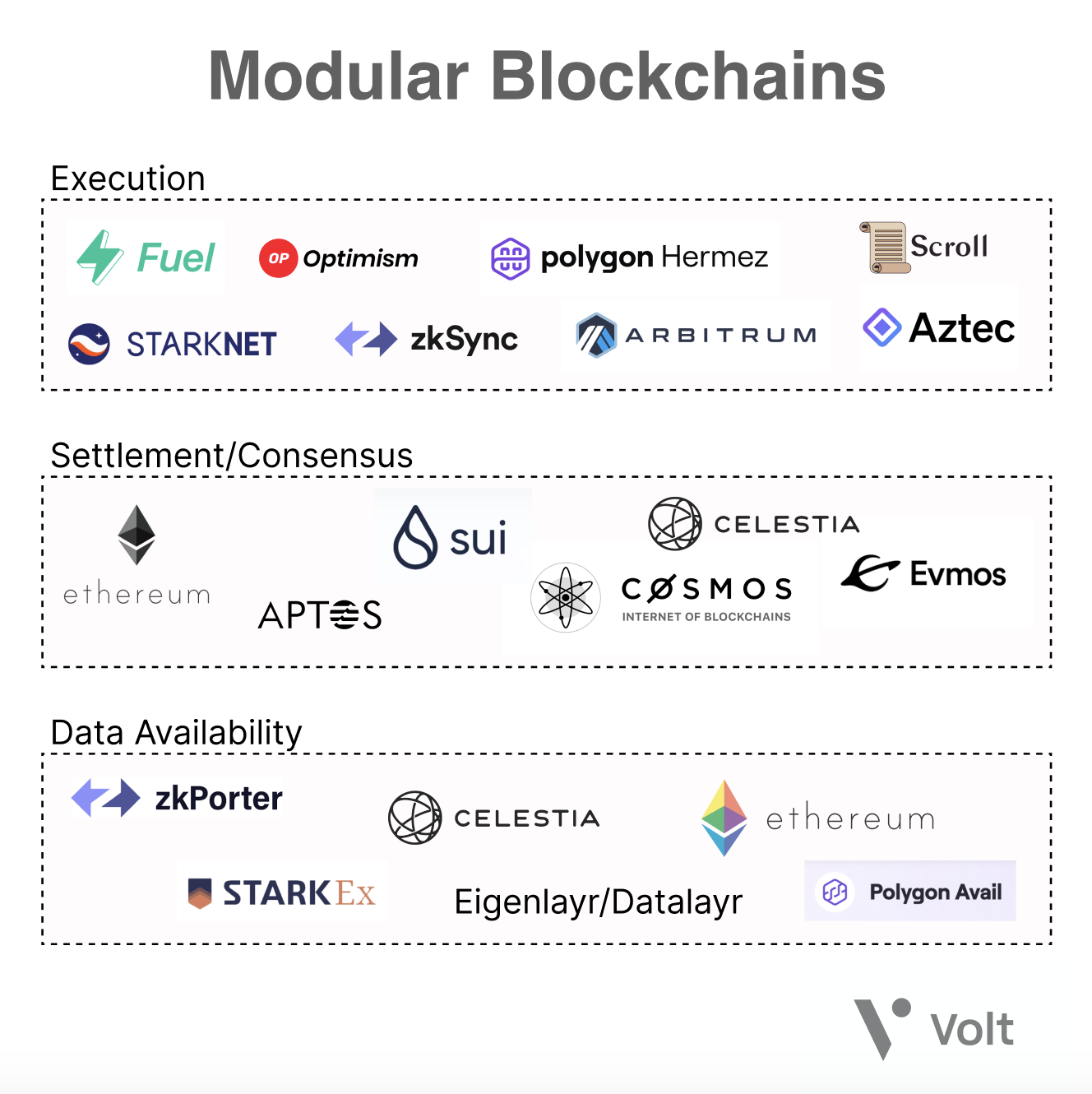
Source: Modular Blockchains: A Deep Dive
1.1.1 Execution Layer
It is responsible for executing transactions and smart contracts. It processes state transitions and updates the blockchain state according to smart contract rules. This layer is further divided into the Execution Environment (EE), a sandboxed area where smart contracts run in isolation, and the Execution Engine (EX) which manages transaction and contract execution within the EE.
1.1.2 Settlement Layer
Settlement layer handles the ordering and finalization of transactions. It ensures transactions are consistently ordered and committed to the blockchain, dealing with aspects like transaction ordering, block production, and conflict resolution.
1.1.3 Consensus Layer
It is responsible for establishing agreement among nodes on the blockchain's state. It ensures all nodes have a consistent view of the blockchain and its history. This layer manages node communication, consensus protocol execution, and fault tolerance, potentially using mechanisms like PBFT or Tendermint.
1.1.4 Data Availability Layer
The fourth is the data availability layer, storing and distributing blockchain data to nodes. It guarantees that all nodes can access the necessary data for validation and execution. Techniques like erasure coding, data sharding, and distributed storage are used for data storage, retrieval and distribution in this layer.
The separation into layers allows each layer to be optimized and scaled independently for improved performance. It enables flexibility for easier upgrades and replacements.

The first of the kind of modular blockchain came out as a L2 rollup on Ethereum, meaning development on the execution and settlement process was the focus. The execution environement in the initial stage was mostly a fork of ethereum’s execution environemnt geth, so the development and research in the proof system, core component in the settlement layer, was crucial in this stage.
The role of the proof system was to introduce a mechanism that permits state changes in L2 after verification. The first optimistic proof system, known as fraud proof, was developed in three main stages. Here is an explanation of the three proof systems used in rollup solutions:
1.2.1 Optimistic Rollups
Optimistic rollups assume that transactions are valid by default. They bundle multiple transactions off-chain and submit compressed data to the Ethereum. During a challenge period, challengers can dispute the validity of the transactions. If no fraud is detected, the transactions are considered final. Optimistic rollups provide faster transaction finality compared to on-chain processing, but require a challenge period before funds can be withdrawn. Examples include OP-Mainnet and Arbitrum One.
1.2.2 ZK Rollups
ZK rollups use advanced cryptographic techniques, specifically zero-knowledge proofs, to ensure the integrity and validity of transactions processed off-chain. The off-chain virtual machine executes transactions, compresses the data, and generates a cryptographic proof that can be efficiently verified on the Ethereum mainchain. This proof confirms the validity of the transactions without revealing their contents. ZK rollups provide faster transaction finality and high-level security, but have higher computational costs for generating the zero-knowledge proofs. Examples include zkSync Era, Scroll, Taiko, and Polygon zkEVM.
1.2.3 Hybrid Rollup
Hybrid rollups combine the strengths of both optimistic and ZK rollups. They leverage optimistic rollups to process transactions off-chain, reducing network congestion and gas costs. Additionally, they integrate zero-knowledge rollups to provide security, fast finality, and more efficient data packing. This hybrid approach aims to optimize Layer 2 networks and expand compatibility with various Layer 1 blockchains. Examples include Metis and Kroma.
Since Celestia proposed the 4 layer model of modular blockchains, the development of each layer has accelerated and numerous new initiatives have emerged.
The execution layer specifies the Virtual Machine(VM), which serves as the environment for processing transactions. Recently, modular blockchains have been integrating a range of VMs into their execution layer, including WASMVM, MoveVM, SVM, zkVM, and ISAVM. These VMs offer advanced functionalities than Ethereum Virtual Machine(EVM), such as support for various smart contract languages, parallelized transaction processing, and specialized environments for zero-knowledge proofs. In this section, we will dive into the diverse execution layers and projects that utilize them.
2.1.1 CairoVM
Cairo and its execution environment, CairoVM, have been developed by Starkware as a part of the Starknet ecosystem. Cairo is tailor-made programming language for STARK-based smart contracts, inspired by the Rust language. Adopting CairoVM for the execution layer offers numerous advantages, especially for validity rollups.
Firstly, the design of Cairo allows for efficient generation of proofs. Its unique architecture, which includes Non-deterministic Continuous Read-Only Random Access Memory, Optimized ISA, and built-in cryptographic functions, optimizes the creation of STARK proofs. Consequently, any program written in Cairo can efficiently produce zero-knowledge proofs to verify its execution's correctness.
Moreover, CairoVM simplifies the development process by allowing developers to write, deploy contracts, and generate proofs without in-depth knowledge of zero-knowledge proofs. This abstraction of the underlying infrastructure enables developers to focus on application logic, enhancing contract security. Additionally, as a Rust-inspired language, Cairo1.0 ensures type and memory safety.
Recently, efforts like Kakarot zkEVM which writes EVM in Cairo have garnered attention, highlighting the growing adoption of CairoVM. As a pioneer in this adoption, Starknet's continued development and expansion are highly anticipated.
2.1.2 WASM VM
WebAssembly(WASM) is an instruction format designed to be a compilation target for high-level programming languages, such as C++, Go and Rust. Codes compiled to WASM have near-native speed with high portability. A WebAssembly Virtual Machine(WASMVM) is the runtime environment that executes WASM code.
Using WASMVM in the execution layer allows for the use of high-level languages that are compilable to WASM. This approach can significantly reduce the cost of contract development. By leveraing WASMVM, developers can write smart contract in languages which is suitable for their application. Furthermore, developers can write smart contracts in languages they are already familiar with, rather than learning platform-specific language.
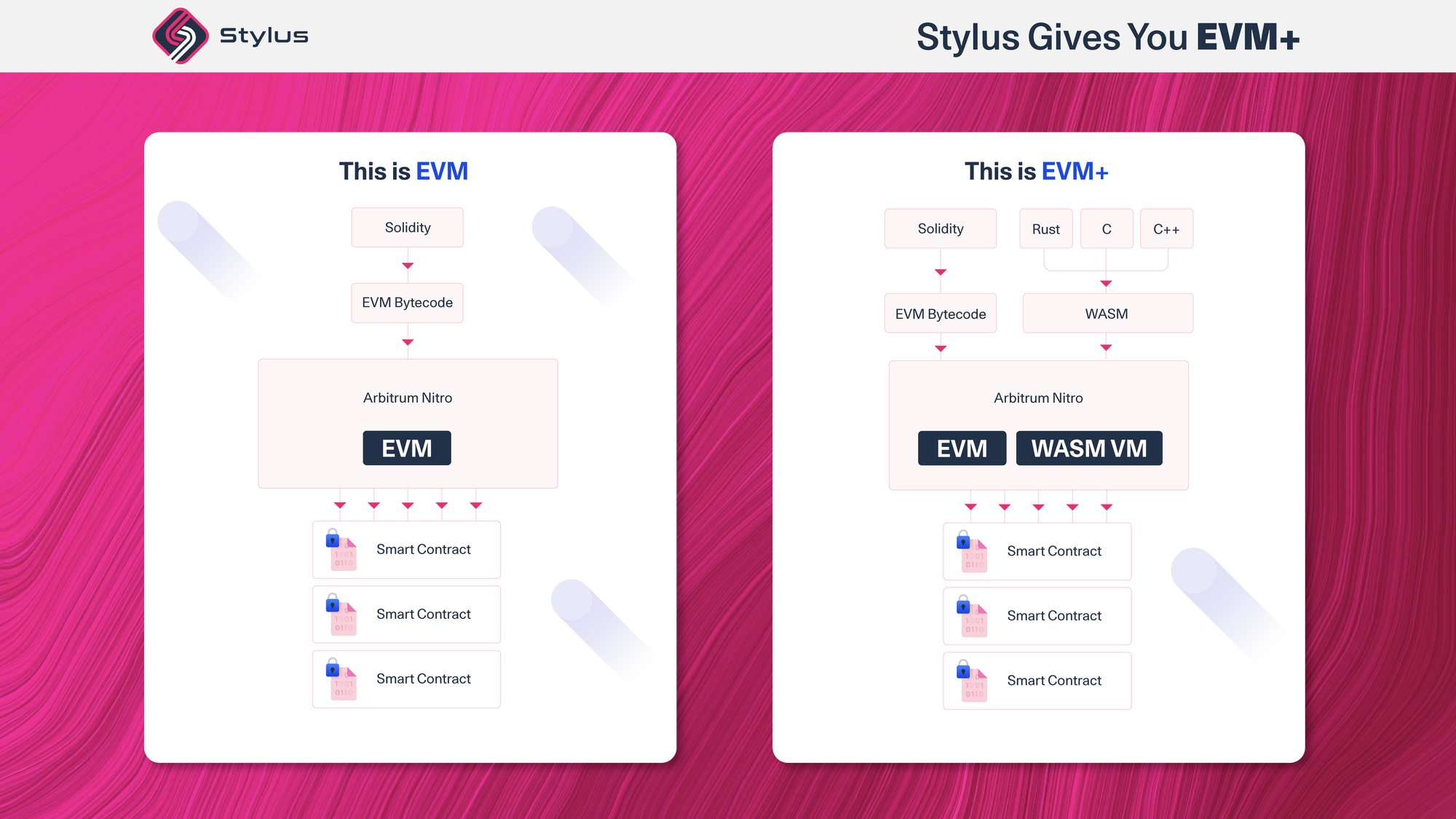
For example, Arbitrum introduced Arbitrum Stylus, which integrates both of WASMVM and Ethereum Virtual Machine(EVM). By offering both VMs, WASM and EVM, Arbitrum Stylus provides a boarder range of languages that developers can choose. This dual VM strategy can leverage both efficiency of WebAssembly and EVM compatibility.
2.1.3 MoveVM
Move is a programming language developed especially for writing smart contracts, with a focus on safety and security. Move introduce a concept of “resources”, which cannot be copied or destructed, similar to native assets. This guarantees that important resources can not be changed or discarded, offering a secure framework for managing digitial assets. MoveVM is the virtual machine in which the bytecode compiled from Move can be executed.
By adopting MoveVM as the execution layer, blockchains can easily derive safety and security of Move. Moreover, MoveVM performs safety checks and validations about bytecode generated from Move program. Using these features, developers can focus more on their smart contract’s logic, without concerning the potential attacks or threats toward their code.
Movement Labs has developed a new framework named Fractal, aiming to utilize both the safety features of Move and the ecosystem of Solidity. By using Fractal, Solidity contract can be easily ported into Move bytecode and analyzed on security vulnerabilities. Based on this Fractal module, Movement Labs has also announced plan to develop a MoveVM-based rollup for Ethereum.
2.1.4 SVM
Solana Virtual Machine(SVM) is Solana blockchain’s execution environment focused on high throughput and scalability for decentralized applications(dApps). Unlike a single-threaded execution model of EVM, SVM runs on a multi threaded environment, using a smart contract parallel processing engine named Sealevel. To efficiently manage and execute multiple smart contracts in parallel, SVM requires smart contracts to explicitly declare the data they will access during execution. By this parallelism, SVM can process a vast number of transactions simultaneously. Furthermore, SVM is register-based and has smaller number of instructions compared to EVM. This design is advantageous for optimistic rollups, as register-based architecture facilitates easier checkpointing. The smaller instruction set is beneficial for zero-knoledge rollups, because it can simplify the proving process.
Eclipse is a Layer 2 for Ethereum which uses SVM for fast transaction processing. By utilizing parallelized transaction execution of SVM, Eclipse can provide lower latency and efficient generation of zero-knowledge fraud proof compared to its competitors.
2.1.5 ISA-VM: General VM
Instruction Set Architecture(ISA) is a set of instructions that defines the interface between software and hardware, such as MIPs and RISC-V. Developers can write program in high level languages and compile it into ISA. ISAVM is a virtual machine that emulates a specific ISA, allowing program written in ISA to run on different hardware platforms.
RISC Zero’s zkVM is an RISC-V ISAVM, which can generate zero knowledge proof about correct execution of RISC-V program. Based on the zkVM, RISC-Zero launched a zkEVM project called Zeth, a RISC-V version of Ethereum builder program which is executable inside the zkVM. Zeth leverages Revm, a Rust-based EVM implementation also used by the popular Rust Ethereum client, Reth, ensuring a high level of compatibility and reusability.
Data Availability(DA) layer is responsible for ensuring that all transaction data is accessible and verifiable. DA layer addresses this data availability problem, which is crucial for security and integrity of blockchain network. The importance of the DA layer is especially highlighted in modular blockchains. Because L2 solutions process transactions off-chain, the transaction data is not directly recorded on L1, making it challenging to verify the completeness and accuracy of the data. Additionally, for L2 solutions to achieve their primary goal of leveraging the security of L1, it’s crucial to accurately transfer data to L1. This is especially important in the case of optimistic rollups that use fraud proofs, because accessing transaction data is nessesary to start challenges. In this section, we explore the ongoing efforts within the Data Availability (DA) layer to ensure data availability.
2.2.1 Avail: The Unification Layer for Web3

Avail is the unification layer of Web3, aiming to unify fragmented ecosystem of blockchain. Numerous successful scalability solutions have emerged, yet they've led to the fragmentation of the ecosystem. The cumbersome of cross-ecosystem transactions has highlighted the need for a solution that allows various rollups to operate as if they were part of a single ecosystem. Avail aims to aggregate multiple rollups (Avail Nexus) based on cutting-edge Data Availability (DA) layer technology(Avail DA), and to enhance cryptoeconomic security by enabling staking with different tokens (Avail Fusion). This so called “The Avail Trinity”, can be a solution for a more unified and efficient Web3 experience.
Avail DA uses a Nominated Proof of Stake(NPoS) consensus algorithm for scalability. It also leverages Substrate’s BABE/GRANDPA framework, which offers rapid block production with proven finality. To enhance data reliability, Avail DA introduces erasure coding. Erasure coding extends data by adding redundancy to the stored data, enabling the reconstruction of data from a subset of the original pieces. This ensures that even if some data pieces are lost or corrupted by malicious party, the original data can still be fully recovered. As an effort to provide data integrity, Avail DA utilizes Data Availability Sampling(DAS) along with KZG polynomial commitments. DAS allows light clients to verify the availability of data through sampling methods. KZG commitmetns provide proofs that ensures the data stored is accurate. By DAS and KZG commitment, light clients can verify the data availability independently and instantly.
Avail Nexus connects vairous blockchains, both within and beyond the Avail ecosystem, based on Avail DA as a modular base layer. Avail Nexus introduces integration standards for rollups, facilitating a seamless Web3 experience across fragmented ecosystem. It aggregates proofs generated by different rollups into one. Therfore, rollups connected to the Avail Nexus can interact each other.
Avail Fusion is designed as a united security layer, which provides security to inherit for rollups. Fusion introduces three kind of tokens can be staked, Avail’s native token, rollup tokens, and foreign tokens. By leveraging the native assets of mature ecosystems such as BTC and ETH, Fusion’s security can be significantly reinforced. Additionally, new rollup tokens created on Avail can enhance sercurity of the base layer. While detailed implementation requires careful consideration of cryptoeconomic security risks, the initiative to leverage tokens from external blockchains to enhance the security of another blockchain is innovative. This approach promises exciting developments in the future.
The fragmentation of the ecosystem is already a significant issue, and the demand for infrastructure that unifies the Web3 environment has always been present. Avail, with its robust base layer known as AvailDA and the technological prowess that has led to its success, seems poised to address this challenge. Given that many rollups are currently utilizing AvailDA as their DA layer, the future of a unified layer led by them is highly anticipated.
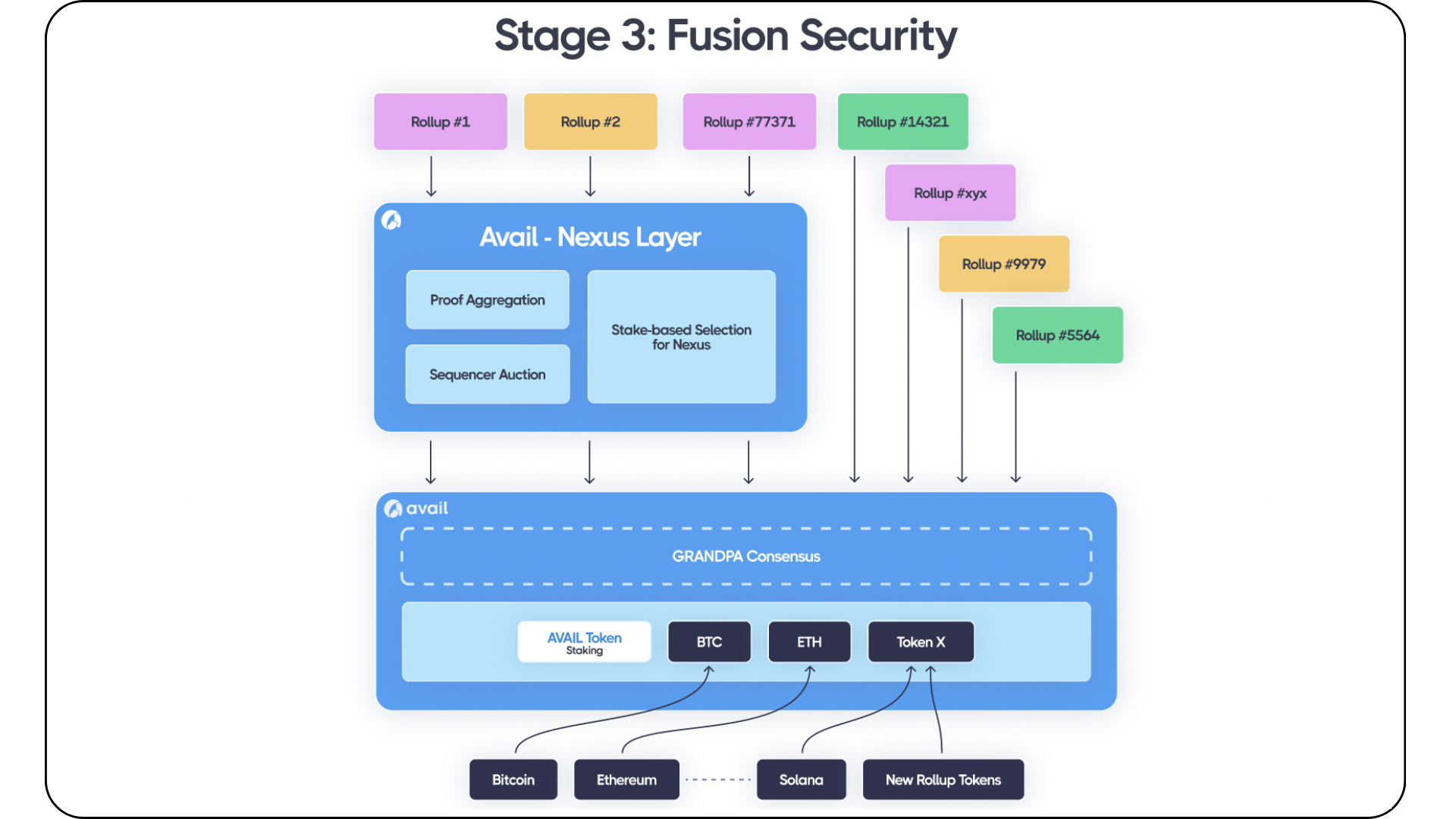
Source: Avail Fusion - Avail Developer Docs
2.2.2 Celestia
Source: Home | celestia.org
Celstia is also a DA layer which is designed to ensure that data is reliably published and can be verified. For data reliability, Celestia uses erasure coding as well. Erasure coding allows data to be stored in a distributed manner, ensuring that the full dataset can be recovered even if parts of it are missing or corrupt. However, to ensure the correct encoding, Celestia uses fraud-proof, which is only needed in challenge period. One of the key technologies used by Celestia is the BlobStreamX. Blobstream is a technology that allows the Ethereum network to verify the availability of stored data. The recently deployed Blobstream X on the Ethereum testnet uses zero-knowledge proofs to convey proofs of data availability to Ethereum. Based on these cutting-edge technologies, Celestia ecosystem boasts over 80 services and applications, including more than 20 rollups.
As Ethereum evolves, data fragmentation has led to on-chain data being dispersed across multiple domains, prompting the development of cross-chain messaging protocols. However, these traditional approaches have problem with bandwidth limitations, increased costs, and bad user experience (UX). The problem arises when many users attempt to transfer data using the same bridging protocol, leading to bandwidth constraints and higher costs. Herodotus aims to address this by utilizing storage proofs that transmit simple commitments to data instead of the data itself.

Herodotus serves as on-chain data access middleware across the Ethereum layers, providing interoperability by offering a secure, fast, and cost-effective way to read data between layers. It uses storage proofs comprised of “Inclusion proofs (the existence of certain data)” and “Computation proofs (specific computations were performed accurately)”. Herodotus has successfully completed a connection from Ethereum to StarkNet and plans to enable bidirectional connections between multiple blockchains in the future. Based on such interoperability solutions, various services can be built:
Governance: Using Herodotus in on-chain voting systems like Snapshot X allows voting with L1 assets on L2 without paying high bridging fees.
Cross-Chain Bridging: Yet Another Bridge offers a bridging service between Ethereum and StarkNet using Herodotus, where asset transfers are performed at the cost of an ERC-20 transfer plus the proving cost.
DeFi: Herodotus enables the use of assets across different domains in DeFi without bridging. For example, assets from L1 can be used as collateral in L2 lending protocols.
Gaming: Another application that can leverage Herodotus’s powerful features is gaming. Users could purchase Gaming NFTs across various Layer 2 platforms and participate in games across multiple domains through cross-chain voting, as mentioned earlier.
Furthermore, Herodotus can be utilized for insurance, account recovery, RANDAO access, and various other purposes, showcasing its versatility and potential in enhancing the Ethereum ecosystem. Herodotus will unify fragmented databases using cryptographic proofs, providing us accessibility to on-chain data.
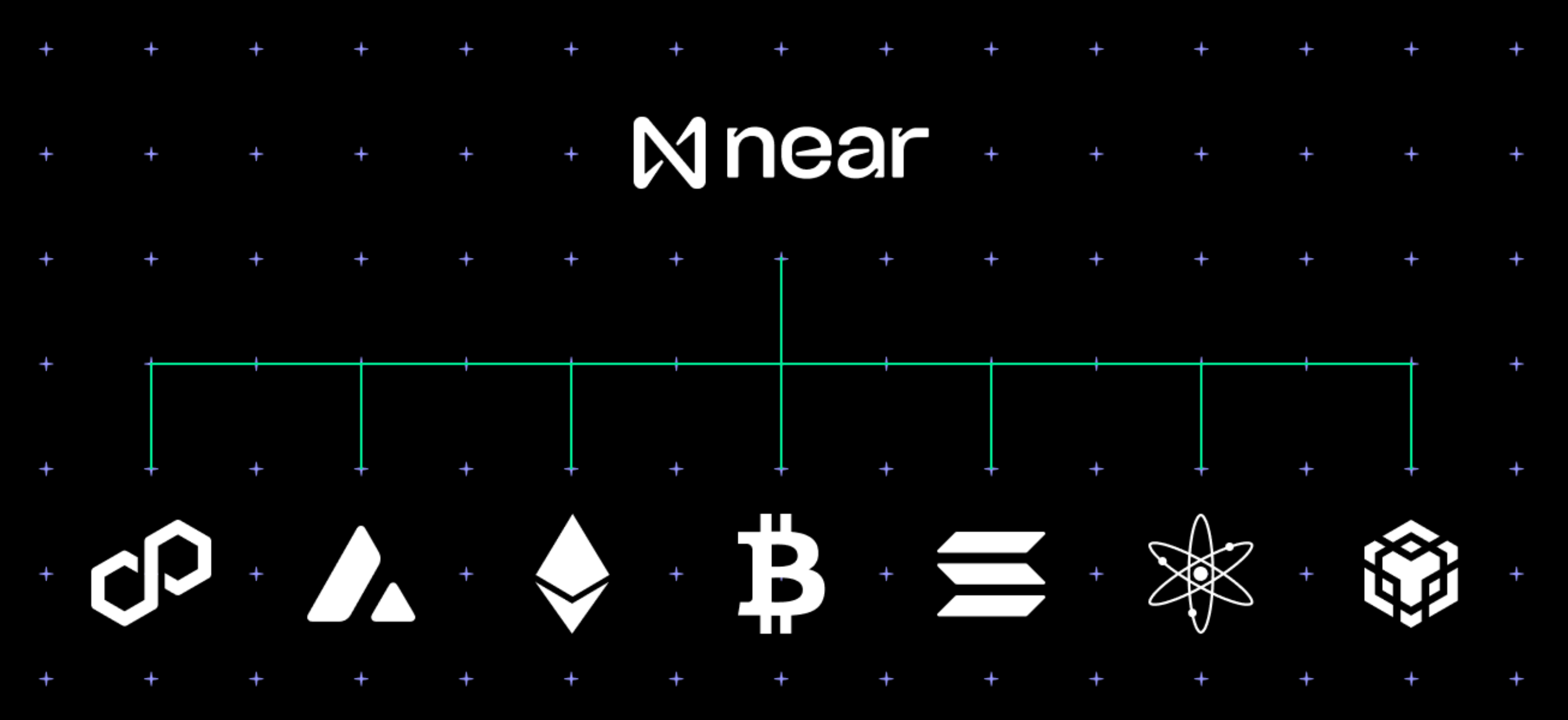
As the concept of modular blockchains has emerged, the blockchain environment has diversified, leading to ecosystem fragmentation as one of the challenges. Near has always been a chain renowned for its excellent usability features, such as native account abstraction and function keys. By extending these characteristics into the multi-chain domain, Near aims to address this fragmentation through Chain abstraction. Chain Abstraction aims to facilitate easy access to a multi-chain ecosystem for users. More specifically, it enables users to seamlessly access multiple blockchains and interact with various chains and rollups using a single account. To implement this idea, the following technologies are being developed.
3.1.1 FastAuth
The transition of Web2 users to Web3 often encounters entry barriers, such as the need to create a wallet and store seed phrases. Near's FastAuth technology supports easy wallet creation and account recovery through email, enabling Web2 users to quickly onboard to the blockchain ecosystem.
3.1.2 Multiple access keys
Near incorporates two types of key concepts: the full access key and the function access key. The full access key allows for asset transfers and broad calling rights for all smart contracts, while the function access key enables calling specific functions of a smart contract. This delegation of certain permissions allows for the implementation of complex service logic without exposing the backend call flow to users.
3.1.3 Meta transaction
Sending a transaction requires paying gas fees in NEAR, but there may be instances where a user doesn't have NEAR. In such cases, users can utilize what's called a meta transaction. For this, users sign an off-chain transaction called DelegateAction and send this message to a relayer. The relayer wraps it into a form that can be processed on-chain and submits it. The on-chain mechanism detects this transaction format and performs the appropriate processing. This way, users can execute transactions without needing to swap assets into NEAR.
3.1.4 Chain Signature
Chain Signature is one of the features offered by Near, enabling users to create and sign transactions on other blockchains through the NEAR network. This process can be broken down into five steps:
Generate the address for the target blockchain using a NEAR address and a derivation path.
Create a transaction that meets the requirements of the target blockchain.
Call NEAR's multi-chain contract to request a signature for the created transaction.
Reconstruct the signature through the response from the MPC (Multi-Party Computation) service.
The relayer transmits the reconstructed transaction to the target blockchain for execution.
The MPC service is a system where multiple nodes share the user's target blockchain private key. Once a sufficient number of these MPC service nodes' signatures are collected, they can generate the user's signature. As several nodes share the secret key, it reduces the possibility of malicious attacks and securely signs transactions on the target blockchain.
3.1.5 Multichain Gas Relayer & Multichain Gas Station
****Multichain Gas Relayer assist users in pre-funding the gas costs required to send multi-chain transactions. They operate in conjunction with the Multichain Gas Station smart contract, which exchanges NEAR for the payment token needed for gas on the target chain. The Multichain Gas Relayer interacts with the external chain's RPC to pre-sign and transmit both the transaction needed for funding gas and the desired transaction by the user. According to official documentation, it currently operates as a centralized server, but the goal is to provide it in library form, allowing direct calls from wallet clients to further decentralize the system.

On the other hand, there exists a Layer 1 that has been developed from the ground up with a focus on rollup infrastructure, which is Initia. Initia has been developed to address the fragmentation within modular blockchains and is also known as the Orchestration layer due to its ability to interwoven multiple Layer 2 solutions. Based on Cosmos-SDK, Initia serves as a Layer 1 platform utilizing optimistic rollup technology to offer a framework for developing and deploying application-specific Layer 2s. The optimistic rollup framework provided by Initia is known as the OPinit Stack, built on the Cosmos SDK. Using Initia offers several advantages.
3.2.1 Cross-Chain Compatibility
Initia provides compatibility with WASMVM, EVM, and MoveVM, allowing Layer 2 solutions to select the VM that best fits their application needs. For instance, MoveVM could be an excellent choice for security-focused DeFi rollups. Additionally, thanks to its compatibility with Cosmos IBC, network interoperability is facilitated, allowing Initia Layer 2s not only to ensure interoperability among rollups within the Initia framework but also to interact with other Cosmos Layer 1s using IBC.
3.2.2 Development Efficiency
Leveraging its rollup framework, which supports a variety of compatibilities (Ethereum, Cosmos IBC, MoveVM, WASMVM, etc.), Initia simplifies the deployment of customized rollups without the developers having to worry about connectivity issues.
3.2.3 Scalability and Security
Initia uses optimistic rollups, making transactions efficient and fast since they need to be verified only once on the main chain. Additionally, as it does not rely on external bridge or oracle services, Initia offers enhanced security.
Initia is targeting a mainnet launch in the second or third quarter of 2024 and plans to release a testnet soon.
While Near and Initia are making efforts as base layers addressing the issue of fragmentation in the multi-chain landscape, there are also teams working at a higher level, focusing on constructing application-specific rollups. These teams represent potential use cases for Near and Initia. Let's explore these efforts further.
3.3.1 Plume Network
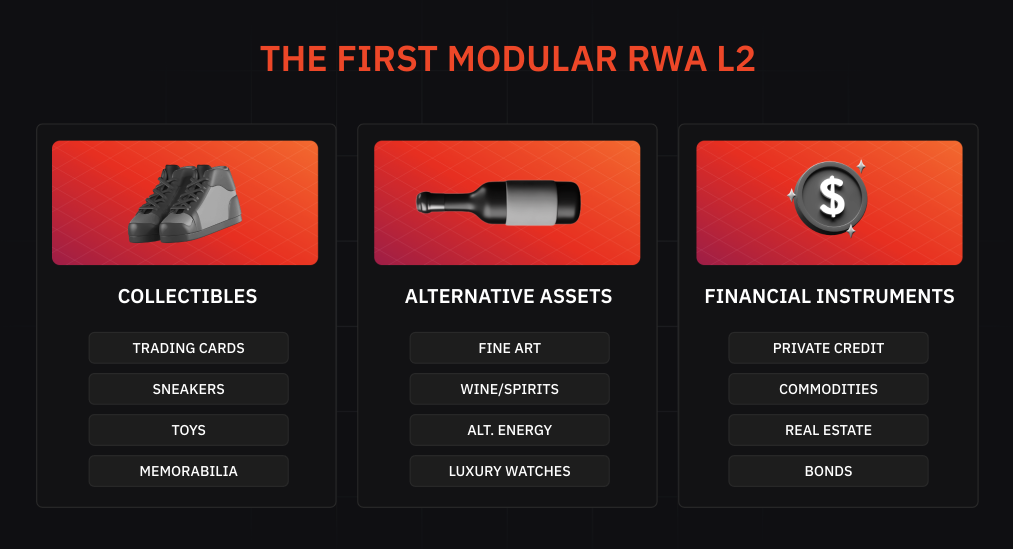
The Plume Network is designed as an L2 solution for Real-World Assets (RWA) with notable features such as:
RWA Tokenization Provider: A key advantage of the Plume Network is its facilitation of RWA token issuance through RWA tokenization providers within the network. These providers ensure compliance with SEC regulations and secure conversion of assets into RWAs. The tokenized assets can then be traded by investors on the Plume Network.
Identity Verification: Plume Network also stands out for offering extensive Identity Verification services, including KYC and KYB. Issuing assets or operating on and off ramps within Plume Network requires providing identity information such as name, date of birth, address, and biometric facial scans to partner companies for KYC processes. Financial service companies looking to issue RWA tokens on Plume Network must verify their identity and legality through the KYB system. Plume Network collaborates with entities like Persona and Sumsub to conduct KYC and KYB, aiming to prevent financial fraud and terrorism financing through RWAs.
AML Monitoring: AML (Anti-Money Laundering) compliance, including adherence to OFAC sanctions, is crucial for financial platforms dealing with RWAs. Plume Network aims to achieve this through continuous transaction monitoring and network analysis, partnering with companies such as Chainalysis and Elliptic.
3.3.2 Kinto

Kinto is a Layer 2 solution tailored for safe and regulated on-chain financial services, characterized by its blockchain-based KYC processes and ongoing AML monitoring. KYC is conducted by KYC providers, and successful users receive a soulbound token, which is a prerequisite for using applications on Kinto. Only wallets holding this token can access the platform's services. Moreover, all accounts are implemented as Account Abstractions (AA), simplifying onboarding for traditional financial users. Technically, Kinto utilizes Arbitrum Orbit and is planning to develop a decentralized sequencer in collaboration with Espresso Systems in the future.
The journey and future of Modular Blockchain have taken various directions, with unique approaches. For instance, Avail and Initia are building the whole stack, alongside some other contributors. Meanwhile, projects like Fhenix and Starknet are improving the execution and settlement aspects of blockchain.
Given that there's always room to improve one component, innovation in the modular blockchain concept will continue. This makes cooperation among projects crucial. We hope this event helped participants to better understand the components and think of ways to enhance their harmony.
Tweets
Theme 1. Past: Advent of the Modular Blockchain [Korean, English]
Theme 2. Present: The Development of Modular Blockchain [Korean, English]
Articles
News
*Special Thanks to all the Co-Hosts David, Brian, Chris, Sang Kim, Bohyun who have organized this wonderful event and Decipher members Yuki and Hyunwoo for their assistance in writing the content.
Thanks to Kate for designing the graphics for this article.
Dive into 'Narratives' that will be important in the next year